In a nine-count US Deparment of Justice indictment filed in an Atlanta federal court in 2017, the four members of the People’s Liberation Army (PLA) in the FBI poster above were accused of hacking into the Equifax credit reporting agency’s systems, creating a massive data breach that compromised the personal information, including Social Security numbers and birth dates, of about 145 million people, nearly half of all US citizens. There is little need but for citizens to read reports in the news media to know foreign intelligence services were operating inside and outside the US with the intention of causing the country great harm. In To Catch a Spy: The Art of Counterintelligence (Georgetown University Press, 2019), James Olson places the efforts of dangerous foreign forces front and center. He explains the efforts being taken by US counterintelligence services to unthread the complicated nature of foreign intelligence activities in the US and drive away the dangers they pose.
There is little need but for US citizens to read reports in the news media to know foreign intelligence services were operating inside and outside their country with the intention of causing the country great harm. In To Catch a Spy: The Art of Counterintelligence (Georgetown University Press, 2019), James Olson places the efforts of dangerous foreign forces front and center. However, more importantly, Olson explains the efforts being taken by US counterintelligence services to unthread the complicated nature of foreign intelligence activities in the US and drive away the dangers they pose. As the former chief of Counterintelligence for the Central Intelligence Agency (CIA), Olson is eminently fitted to represent US counterintelligence officers and present their work. In defining counterintelligence, Olson states that it “consists of all the measures a nation takes to protect its citizens, secrets and technology from foreign spies.” Reportedly, over the years 80 countries, to include allies and friends, have engaged in espionage operations against the US.
As with all other elements of the intelligence industry, counterintelligence work requires wisdom, reason, and logic to be performed well. It is not the nature of intelligence services to regularly use aggression and force to halt an opponent, shut down its networks, thwart its operations, and intercept its intelligence officers, operatives, and informants. The intellect is the tool used for doing so.
From what Olson explains, counterintelligence organizations worldwide must detect necessary attributes of an actor, certain indicia, before initiating a counterintelligence investigation on a suspected “foreign spy” or operative or informant or foreign intelligence service. The primary means to confirm their identity is through careful study and observation of the subject and thorough research of all available information. It is a process similar to selecting a target for recruitment. That process may not always be easy going. A foreign intelligence officer’s tradecraft may be superb and all of his or her interactions and moves might appear authentic. The foreign intelligence officer’s movement technique could make maintaining surveillance on the subject difficult. For any counterintelligence services, that type of professionalism in an opponent can pose a challenge. Oddly enough though, it will result in increased suspicion among some. Counterintelligence may very well be the greatest manifestation of the paranoia business.
Regarding his career, again, for over thirty-one years, Olson served in the Directorate of Operations of the CIA, mostly overseas in clandestine operations. He was deployed overseas for several assignments, and eventually became chief of counterintelligence at CIA headquarters in Langley, Virginia. At the time he wrote To Catch a Spy, he was retired and working as a Professor of the Practice at the Bush School of Government and Public Service of Texas A&M University. Robert Gates, the former Director of Central Intelligence, 1991-1993 remarked about Olson: “James Olson is a legend in the clandestine service, having served in some of the most difficult, dangerous, and complicated assignments at the height of the Cold War. As director of Central Intelligence, I trusted him without reservation when he was chief of counterintelligence not only because he was enormously capable but also because I knew he thought deeply about the ethical and moral dimensions of what we did every day. Amid the countless books and memoirs of retired spies, especially at this time, this one is essential reading.” Olson was born and raised in Iowa. He studied mathematics and economics at the University of Iowa. Following college, he took a commission in the US Navy, serving aboard guided missiles destroyers and frigates. After a period, he would return to Iowa to study law at the University of Iowa. Apparently, Olson had every intention of practicing law in a small county seat town in Iowa. However, the CIA approached him and invited me to apply for a position in the clandestine service.That us when the story of his life in counterintelligence began.
This book has immediate historic significance because Olson is recognized as an authority among intelligence circles worldwide. There are not so many that have been written so well by former professionals. While others may have their preferences, three of special note and highly recommended by greatcharlie are: Raymond Batvinis, Hoover’s Secret War Against Axis Spies: FBI Counterespionage During World War II (University Press of Kansas, 2014); David Martin, Wilderness of Mirrors (HarperCollins, 1980); and, Scott Carmichael’s True Believer: Inside the Investigation and Capture of Ana Montes, Cuba’s Master Spy 1st ed. (Naval Institute Press, 2007) which Olson refers to in To Catch a Spy.
In Hoover’s Secret War Against Axis Spies–reviewed by greatcharlie on April 30, 2014, the historian, Batvinis, a former Federal Bureau of Investigation (FBI) special agent, presents a crucial chapter in the history of World War II during which the FBI really began and refined its counterintelligence mission. He discusses the FBI’s then new reliance on intrusive investigative techniques (wiretaps bugs, access to bank and financial transaction records), and the evolution of the Bureau’s liaison relations with the British, Canadian, and US military intelligence agencies. (In a proceeding book, his acclaimed, Origins of FBI Counterintelligence (University of Kansas, 2007), Batvinis went off from scratch to tell the reader about the situation.) In Wilderness of Mirrors, Martin tells the story of how an ex-FBI agent William “King” Harvey identified the notorious Soviet double agent Kim Philby in conjunction with James Jesus Angleton, the CIA’s chief of counterintelligence responded to the betrayal of family friend Philby’s betrayal and descends into a paranoid wilderness of mirrors. Wilderness of Mirrors set a benchmark for studies, memoirs, and all other written works on US counterintelligence. It was once required reading for some intelligence professionals–and perhaps it still is. The author of True Believer, Carmichael, was a senior security and counterintelligence investigator for the Defense Intelligence Agency and the lead agent on the successful spy hunt that led to Ana Montes. He provides an inside account of how his espionage investigation, with the eventual help of the FBI, progressed over a period of several years to develop a solid case against Montes. She is the only member of the US intelligence community ever convicted of espionage for the Cuban government. Every twist and turn is all the more intriguing as truths become lies and unlikely scenarios are revealed as reality.
To Catch a Spy is not Olson’s first book. He is also the author of Fair Play: The Moral Dilemmas of Spying (Potomac Books, 2006) Fair Play examines ethical challenges facing US intelligence officers as they attempt to operate within a standard of acceptable moral behavior. That examination is couched in an insightful summary of intelligence history through fifty reality-based scenarios.
To Catch a Spy, 248 pages in length, was released by Georgetown University Press on April 11, 2019. Since then, many others have already formed their own opinion of Olson and his work. For those who may excavate through To Catch a Spy to thoroughly consider points of exposition concerning both himself and activities in which he was engaged, the book has doubtlessly been substantially edifying. The reader is provided with an amazing opportunity to see it all through the prism of a master craftsman as he discusses his profession. Indeed, as with Fair Play, everything Olson provides in To Catch a Spy is founded on his experience during a lengthy career in US counterintelligence. Nevertheless, To Catch a Spy is not a memoir of his life or of his career. That has yet to be written, and perhaps may not be. Still, if one were to go off anyway and measure Olson’s book against the memoirs of Cold War Soviet, Eastern Bloc adversaries of the US there is a decided difference. Those memoirs have a tendency to be anecdote laden, picturesque and exciting. While those who have professionally analyzed them judge them as omitting much, their books typically provide enough nuance to allow for extrapolation, inference, and conceptualization of their tactics, techniques, procedures, and methods. They also often point to their bad choices, pitfalls and ways to minimize losses after encountering them, commonplace wrong turns and remedies to them. That is really what the neophyte needs to receive most.

The author of To Catch a Spy, James Olson (above). Olson is eminently fitted to represent US counterintelligence officers and present their work. For over thirty-one years, Olson served in the Directorate of Operations of the Central Intelligence Agency (CIA), mostly overseas in clandestine operations. He was deployed overseas for several assignments, and eventually became chief of counterintelligence at CIA headquarters in Langley, Virginia. In defining counterintelligence, Olson states that it “consists of all the measures a nation takes to protect its citizens, secrets and technology from foreign spies.” Reportedly, over the years 80 countries, to include allies and friends, have engaged in espionage operations against the US.
Surely for readers thrilled by spy novels, there was enough provided by Olson to allow them to live vicariously through his anecdotes. In the genre of fiction and nonfiction spy stories, there is an artistic milieu in which–often under the demands of publishers who are intensely interested in selling books–writers seek to position themselves amidst. It cannot be denied that human nature instinctively finds entertainment more compelling than edification. Perhaps even among them, there may be some who will decide after reading To Catch a Spy, that there is nothing so outré about counterintelligence. However, often things seem simple once they have been explained.
Among professionals, not only in the US, but worldwide, To Catch a Spy was likely anticipated with baited breath. That stands to reason that this category of reader would be aware that Olson possesses a huge body of thoughts that most US counterintelligence officers on the job today. There was considerable satisfaction among professionals with his first book, Fair Play. They could have only imagined that To Catch a Spy would be another gem. One might perceive while reading To Catch a Spy that Olson subtly takes on the role of instructor, introducing somewhat nuanced details about certain matters in his lecture as if he were trying to impart the full benefit of his experience to prescient, young CIA counterintelligence officers. To that extent that he does all of this, there is a trace of something akin to a pedagogy for developing the reader’s understanding of the world he is moving them through. A quote widely attributed to one of the most influential artists of the 20th century, Pablo Picasso: “Learn the rules like a pro so you can break them like an artist.” To that extent, novice US counterintelligence officers must master the fundamentals, and the foundation will be laid to explore one’s potential with confidence and an assured step with knowledge and experience of those who came before.
One might expect copies of To Catch a Spy, that may be possessed by US counterintelligence officers from the various services, are treasured and well thumbed. Spotted among reviews of the book on Amazon.com are comments from US intelligence officers in which they attest to the value, positive impact To Catch a Spy had on their thinking and their work. Alex J. Vega IV, Joint Counterintelligence Training Activity (JCITA), Defense Intelligence Agency, and Former U.S. Army Attaché, U.S. Embassy, Moscow, Russia wrote: “Jim Olson has shared with us his accumulated wisdom, lessons learned, and roadmap for the future. To Catch a Spy is the new U.S. counterintelligence standard. It is a must read for serious professionals and anyone interested in the spy world. Jim has done a tremendous service, not only to our generation, but also to those of the next who choose to answer the call to join the counterintelligence battle.” Henry A. Crumpton, a twenty-four-year CIA veteran, author of The Art of Intelligence: Lessons from a Life in the CIA’ s Clandestine Service (Penguin Press, 2012), and CEO of Crumpton Group LLC. remarked: “The author, America’s counterintelligence guru, has crafted a remarkable, indispensable book rich in heartbreaking detail and sharp analysis–serving as a clarion call for a stronger response to the unrelenting, sophisticated, and successful foreign espionage assault on our nation.” Robert M. Gates, Director of Central Intelligence, 1991-1993, stated: “Amid the countless books and memoirs of retired spies, especially at this time, this one is essential reading.”
One could safely state that To Catch a Spy has not been everyone’s cup of tea. Despite such glowing expressions of satisfaction and appreciation, there is a view of the book in which it is asserted that Olson really did not dig down so deep on issues in the text to display his full capabilities as a counterintelligence thinker. He could hardly be so profound, or candid at all. Some professionals worldwide who may have acquired a copy of To Catch a Spy were disappointed when they discovered that the text is not heavy with inferences and insights, and analysis supported by references. In fact, such are rather sparse in the book. In Mark Soares’ review of the book in the scholarly journal Intelligence and National Security, (Mark Soares (2020) To Catch a Spy: The Art of Counterintelligence, Intelligence and National Security, 35:7, 1079-1081, DOI: 10.1080/02684527.2020.1746125), he begins by saying: “James M. Olson has written a deeply personal composition of his extensive career to counterintelligence with the Central Intelligence Agency (CIA) using a loose and relaxed format not typically seen in intelligence literature.” Explaining Olson’s purpose in writing the book, Soares remarked: “To Catch a Spy serves as Olson’s caution to future US intelligence practitioners and to his country as a whole to pay far more attention to counterintelligence matters rather than focusing all efforts on collection.” However, Soares would eventually judge the book critically, stating: “Though To Catch a Spy is undoubtedly an entertaining read, scholars and academics will be disappointed by the absence of references, with Olson opting instead to use informal notes to add background details to organizations, individuals, tradecraft terms, or historical events mentioned in the book (pp. 203-217). Many of the events described by Olson could have been referenced more properly given the abundance of information available on such topics.”
For security reasons, Olson admits to having doffed his cap to his former employer so to speak by submitting To Catch a Spy to his former employer, CIA, for review. It is a requirement for officials from the US Intelligence Community with backgrounds as Olson. In Olson’s case, his former employer’s solemn warning of secrecy was increased with regard to the knowledge he retained as any information that would provide some nuance on how the US detects and catches spies would be of the utmost interest and importance to the foreign intelligence services of adversaries as well as allies. One can only imagine an individual with his wealth of knowledge is holding back considering how much more he could have potentially ruminated upon in the book. Under such circumstances, it is understandable that Olson’s lack of profundity would disconcert some.
If Olson were writing only for intelligence professionals, he would have a diminutive audience. While some US counterintelligence professionals might nonetheless view it as their book, To Catch a Thief is a book published for the largest audience possible. To that extent, Olson does not take for granted how much the reader can absorb from what he teaches. It is evident that he takes control of that process, apportioning how much of the story he feels would be appropriate. When he feels the reader should be ready for more, Olson increases the quantity and complexity in his anecdotes.
Even after what could be sardonically characterized as Olson’s generous effort to spoon-feed some readers, other concerns about how the book was written were voiced by reviewers from outside of the profession. In the New York Journal of Books, Michael McCann wrote: “To Catch a Spy struggles to the finish line far behind many other, better publications in terms of immediate relevance. Which invites an important question: Who is Olson’s intended audience?” On that point McCann goes on to state: “To Catch a Spy will provide a useful textbook for students taking Olson’s courses at the Bush School. No doubt they will be quizzed on his ten commandments, the three principles of workplace counterintelligence, and other key points. It will also help them write summaries of important counterintelligence cases over the years and the lessons learned from them.” Leaving no doubt that he was disappointed by the book, McCann states: “For the general reading public, however, To Catch a Spy doesn’t really appeal. Those looking for “juicy new disclosures” will be disappointed as they wade through material just as easily accessed at no cost by googling for it online.”
In its review, greatcharlie, using its understanding of the subject as a nonpracticioner, observing from outside the bureaucracy, follows those aspects of the book closely. The last outcome greatcharlie wants is for its review to boil down to discussion of “Olson left this out. He left that out. He did not elaborate enough here or there.” Despite any concerns about what was missing in the text, in its review of To Catch a Spy, greatcharlie explores what one can appreciate and learn about Olson’s thinking process from what he does provide in the text. However, what is most impressive about To Catch a Spy to greatcharlie is the manner in which it stimulates thought on the issues presented. Books that can stir a fire inside the reader, and a passion for a subject, are the most memorable and most enjoyable to sit with. To that extent, included in the review are greatcharlie’s own thoughts about counterintelligence topics covered by Olson which hopefully will assist some readers in better understanding what Olson is presenting to them. It is also hoped that thoughts shared by greatcharlie will encourage readers to weigh their own impressions on those topics and develop of their own insights on them whether they may be actual intelligence practitioners or just enthusiasts. Additionally, greatcharlie offers its own thoughts on those topics to assist in giving context to the work of US counterintelligence to the US public, nonprofessional readers, in particular, and, in turn, offer some perspective to the counterintelligence professional on how the ave4age US citizen perceives his or her work. With any luck, what is presented will appropriately resonate among both sets of readers. Rationale enim animal est homo. (Man is a reasoning animal.)

The Headquarters of the Russian Federation SVR in Yasenevo (above). The first three chapters of To Catch a Spy form a compendium of efforts Olson spotlights of respective Chinese, Russian, and Cuban foreign intelligence services against the US. This is a matter that absolutely merits treatment particularly for the sake of the intelligence enthusiasts and the nonpracticioner. It is great that Olson broached the matter early in his book. The intelligence services of China, Russia, and Cuba are driven by the same concepts and intent that typically drive the leadership of their respective authoritarian countries: greed, cruelty, and lust for power, even world domination. It is fairly well-known outside of the intelligence world that China has concerned the US greatly of late. Olson’s compendium of adversarial intelligence services activities essentially provides a run down of those respective adversaries’ intelligence operations, both successes and defeats. Much of the information on the cases used to support any small assertions by Olson on the nature of these adversaries’ respective efforts has already been made public. In fact, they were presented in some detail via US Department of Justice indictments and criminal complaints for those cases.
Country Reports on the Main Adversaries of the US
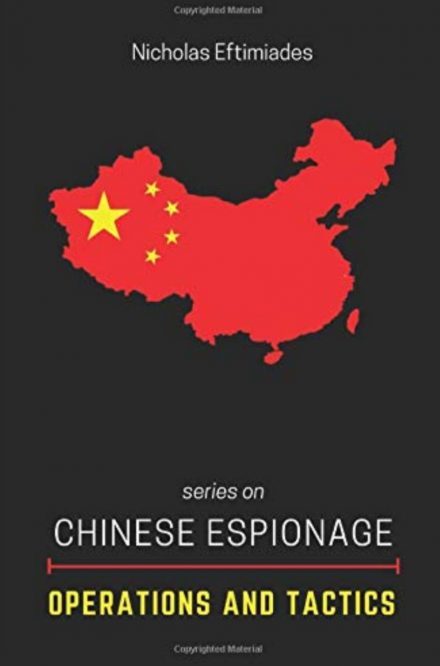
The first three chapters of To Catch a Spy form a compendium of efforts Olson spotlights of respective Chinese, Russian, and Cuban foreign intelligence services against the US. This is a matter that absolutely merits treatment particularly for the sake of the intelligence enthusiasts and the nonpracticioner. It is great that Olson broached the matter early in his book. The intelligence services of China, Russia, and Cuba are driven by the same concepts and intent that typically drive the leadership of their respective authoritarian countries: greed, cruelty, and lust for power, even world domination. It is fairly well-known outside of the intelligence world that China has concerned the US greatly of late. Olson’s compendium of adversarial intelligence services activities essentially provides a run down of those respective adversaries’ intelligence operations, both successes and defeats. Much of the information on the cases used to support any small assertions by Olson on the nature of these adversaries’ respective efforts has already been made public. In fact, they were presented in some detail via US Department of Justice indictments and criminal complaints for those cases.

Suspected spy for the Communist Party of China, Christine Fang (above). It was revealed in 2020 that Fang had established contacts and some relationships with several political officials from mayors and local council members, to Members of the US Congress as part of an effort by China to infiltrate US political circles. Olson explains that the Chinese have been trying to influence US political campaigns through illegal contributions since at least the 1990s. Olson says China is in a class by itself in terms of its espionage, covert action, and cyber capabilities. He admitted the US was not doing enough now to prevent China from stealing its secrets. Olson reports that the goal of China’s massive espionage, cyber, and covert action assault on the US is to catch up with the US technologically, militarily, and economically as quickly as possible.
China
Olson explained that China is in a class by itself in terms of its espionage, covert action, and cyber capabilities. He admitted the US was not doing enough now to prevent China from stealing its secrets. Olson explains that the goal of China’s massive espionage, cyber, and covert action assault on the US is to catch up with the US technologically, militarily, and economically as quickly as possible. Olson asserts that if the average US citizen fully understood the audacity and effectiveness of this campaign, they would be outraged and would demand action.
There were four important disclosures by Olson on Chinese espionage, which, despite claims from some reviewers were well-known, in greatcharlie’s view can at least be said to have been given “proper” additional light in his discussion. They include the restructuring of the Chinese intelligence services, the political work they do in the US, concerns that a possible mole is ensconced in the US Intelligence Community, and again, the enormity of Chinese espionage. Regarding the Chinese intelligence apparatus, he explains that it was restructured in 2015 and 2016. The principal Chinese external intelligence service is the Ministry of State Security (MSS)., which is responsible for overseas espionage operations. The Ministry of Public Security (MPS) concentrates on domestic activities but also occasionally runs agents abroad. The MSS and MPS were relatively unaffected by recent organizational changes in the Chinese intelligence community. The major impact has been on the People’s Liberation Army (PLA), which since the 1950s has been heavily engaged in intelligence operations. The PLA in theory has concentrated on military intelligence, but it has actually defined its role more broadly. Olson reports that it has competed with the MSS in a wide range of economic, political, and technological intelligence collection operations overseas, in addition to its more traditional military targeting. The PLA is still responsible for the bulk of China’s cyber spying. However, Olson points to indications that the MSS has been assigned an expanded role in this area as well. Concerning how it is all organized, Olson reveals that the PLA’s human intelligence (HUMINT) operations are managed by the Joint Staff Department, and comes under the Central Military Commission. The previous breakdown of the PLA into intelligence departments has been eliminated. Oversight of the PLA’s technical intelligence like certainly capabilities (including cyber, signals, and imagery intelligence) resides with the new Strategic Support Force under the Central Military Commission.Thus, the Second Department of the People’s Liberation Army (2PLA), responsible for human intelligence, the Third Department of the People’s Liberation Army (3PLA), the rough equivalent of the National Security Agency (NSA), responsible for cyber operations, and a Signals Intelligence, or a Fourth Department of the People’s Liberation Army (4PLA), responsible for electronic warfare have been rolled into the new Strategic Support Force. Olson explains that much as all intelligence services worldwide, both the MSS and the PLA make regular use of diplomatic, commercial, journalistic, and student covers for their operations in the US. They aggressively use Chinese travelers to the US, especially business representatives, academics, scientists, students, and tourists, to supplement their intelligence collection. Olson takes the position, disputed by some experts, that Chinese intelligence services take a vacuum cleaner approach and collect literally any kind of data they can get their hands on in the US.
Olson explains that the Chinese have been trying to influence US political campaigns through illegal contributions since at least the 1990s. He points to the huge row raised in 1996 when the Washington Post reported that the US Department of Justice was investigating possible illegal Chinese contributions to the Democratic National Committee (DNC) in an effort to influence both the Presidential and Congressional election that year. After getting into a handful of pertinent details about two Chinese businessmen, Johnny Chung and John Huang, Olson explains that the FBI determined that the 1996 illegal funding operation was coordinated from the Chinese Embassy in Washington. Olson says the issues at stake for the Chinese government are not difficult to devine: US support to Taiwan, intellectual property law, trade policies, the environment, human rights, and Asian security. China denied any role in the influence buying. Going a step further, Olson warns that candidates of both political parties have been targeted for influence buying. Chinese hackers have been detected in the campaign websites of both candidates in every presidential election since 2000, another indication that the threat of Chinese election tampering has not gone away. In 2016, Virginia governor Terry McAuliffe was notified by the US Department of Justice that he was the target of investigation for allegedly accepting a questionable campaign contribution of $120,000 from Chinese businessman Wenqing Wang. McAullife was not charged with any crime. There has been considerable controversy lately about alleged Russian tampering in the US presidential Election of 2016. Such allegations, Olson duly notes, should be investigated thoroughly, of course, but he points out that the Chinese have been engaged in such activities for 20 years.
Olson notes that in a May 20, 2017 New York Times article informed that 18 to 20 of the CIA’s best spies inside China had been imprisoned or executed. The New York Times based its information on “ten current and former American officials” who chose not to be identified. According to Olson, the losses actually occurred between 2010 to 2012 and effectively wiped out the CIA’s excellent stable of assets inside the Chinese government. Olson proffers, “If true, this disaster is eerily reminiscent of the decimation of the CIA’s Soviet agent program in 1985.” The fact that Olson would even discuss the New York Times report in To Catch a Spy, gives the story far greater credence than it would have otherwise. With regard to what occurred from 1975 to 1985, the CIA built up a remarkable inventory of well-placed agents inside the Soviet Union–only to see them disappear, one by one, because of what Olson describes “the perfidy” of Edward Lee Howard and Aldrich Ames. According to the New York Times report, the CIA’s counterintelligence theories about what went wrong in China have mirrored the same avenues that it explored after 1985. Olson laid out a few of the questions that were asked by US counterintelligence services: “Could our compromises have been the result of sloppy tradecraft? We’re we being beaten on the street? We’re our secret communications being intercepted? Or did we have a mole?”
Olson says arrests in rapid succession in a compressed period usually point to a mole. In fact, a former CIA case officer, Jerry Chun Shing Lee, was arrested by the FBI in January 2018 and charged with espionage. After Lee left the CIA in 2007, he moved to Asia with his family and was doing business there. In 2010, he was allegedly approached by Chinese intelligence officers. If, as alleged, Lee gave up the identities of CIA spies in China, Olson believes he either took notes with him when he left the agency in 2007 or remembered who they were. Olson reports that the FBI, as part of its investigation, was looking closely at deposits made to Leeds bank account. It took 9 years to catch Ames. Olson states: “I hope it will not take that long to figure out what happened in China and, if the problem is in fact human, to bring the traitor to justice.
Olson submits to the reality that enormity of the Chinese espionage effort is staggering, noting that the FBI announced in 2015 that it had seen a 53 percent increase in economic espionage against US companies over the previous year, and most of it from China. US companies remain extremely vulnerable despite being aware of the Chinese threat. According to Olson, the MSS and PLA primarily play the ethnic card in their recruitment operations. They target a large number of ethnic Chinese–the “overseas Chinese”–who live in the US and virtually every other country in the world. Still, the MSS and PLA would also engage in nonethnic recruitment of US citizens. Those nonethnic recruits, Olson says are few in number, have done serious damage given reports on their activities.
Olson presents the statistic that approximately 4 million ethnic Chinese in the US are only a generation or less from the mainland and great numbers of them still have relatives in Communist China. He says many of them also still feel pride and sympathy for the culture and accomplishments of China, particularly the build up of economic and military strength under Mao and his successors. Olson states that the common tactic is to play on loyalty to Mother China and to exert pressure via relatives still living in China. A Chinese-American working in the US government or in a high-tech firm would usually be approached on that basis, but he notes that venality and greed can also play a large role in any recruitment of a spy. Olson says that all US citizens who visit China are assessed as potential recruitment targets–and those who he access and show susceptibility are singled out for aggressive development. To emphasize how well Chinese recruitment efforts work, Olson provides a partial listing of Chinese-Americans who have fallen to this trap, the information they were instructed to collect, and where they were located: US Navy Lieutenant Commander Edward Lin, caught providing classified military information; Szuhsiung Ho, caught recruiting six other US engineers to provide nuclear technology to China; Peter Lee, caught providing naval technology and defense information to China; China Mak, caught passing classified information on surface ships and submarines; Fe Yei, caught stealing computer microprocessor technology for China; Walter Lian-Heen Liew, caught providing chlorides-route titanium dioxide production technology to China; and, Greg Chang, caught providing proprietary information on the US space program to China. Olson then devotes a page and a half to the case of Katrina Leung, whose objective was not to steal technology but to infiltrate US counterintelligence. His account provides less about tradecraft, having been errantly recruited by the FBI as a counterespionage agent, she used and told more about the details of her relationship with two FBI counterintelligence officers, James Smith and William Cleveland.
As for nonethnic recruits of the MSS and PLA, Olson presents summaries of the cases of Benjamin Bishop, caught passing classified defense information to his young Chinese girlfriend; Candace Claiborne, having served in Shanghai and Beijing as a State Department employee, she was caught cooperating with Chinese intelligence; and, Glenn Duffie Shriver, recruited by MSS while visiting China as a student was caught delivering stolen military technology to his intelligence handlers. Curiously, even though Olson explains that he has presented only a partial list of ethnic and nonethnic recruits caught by US counterintelligence services, the list appears rather diminutive given his own admission that there is a vast Chinese intelligence collection effort currently underway in the US. There would surely be some reason for US counterintelligence services to be proud of the outcome of investigations into the activities of those captured. However, far more will need to be done before they begin to even stem Chinese espionage in the US. (A discussion of the transition from ethnic to non-ethnic recruitment by can found in greatcharlie’s July 31, 2020 post entitled “China’s Ministry of State Security: What Is this Hammer the Communist Party of China’s Arm Swings in Its Campaign against the US? (Part 1).”
Olson touches on two recurring themes in discussions on Chinese intelligence: students and cyber attacks The question of Chinese students in the US, is especially pertinent. According to another statistic that Olson offers, in 2016-2017 there were 350,755 Chinese nationals studying at US colleges and universities, accounting for approximately one third of the total of international students in our foundry. He points to that fact that a large majority of Chinese students are studying science or engineering, fields that have direct relevance to China’s industrial and military aspirations. Olson reveals that many Chinese students are encouraged by Chinese intelligence to remain in the US, to obtain employment, and to acquire lawful permanent resident status. Lawful permanent residents can apply for US citizenship after five years of residence, three years if they are married to a US citizen. Naturalized US citizens are eligible for US government security clearances after five years of citizenship. Olson says these regulations represent a trade off between our need for certain skills–particularly technical skills–and security. Olson notes that the US Intelligence Community feels any intelligence service worthy of the name would jump at the chance to infiltrate its officers and co-optees into government agencies, national laboratories, and high technology firms of a priority target country. While admitting that he had no data to support that position, he says it is inconceivable to him that the MSS and PLA would have overlooked this enticing and easily exploitable path to access.
Regarding cyberattacks from China, Olson notes that they are nothing new. The first major attack was discovered in 2005, but it was quickly determined that infiltrations of US government computer networks had been going on since at least 2003. Olson relates that the 2003 operation, dubbed Titan Rain, was a coordinated attack by Chinese cyber spies to download sensitive Data from networks at the US Departments of Defense, State, Energy, and Homeland Security, as well as a host of US defense contractors. In one day, the hackers stole reams of sensitive aerospace documents with schematics of propulsion systems, solar paneling, and fuel tanks for NASA’s Mars Reconnaissance Orbiter. Other targeted locations included the US Army Information Engineering Command, the Naval Oceans Systems Center, the Missile Defense Agency, and US national laboratories. Olson says cyber attacks such as Titan Rain present a unique challenge in terms of attribution. In the case of Titan Rain, however, Olson explains that it is not credible to conclude that a multifaceted and sophisticated operation of this magnitude could be anything other than a Chinese government-sponsored activity.
In 2010, Google announced that the company had detected a “highly sophisticated and targeted attack on [its] corporate infrastructure originating from China that resulted in the theft of intellectual property from Google.” While China’s involvement in cyber attacks was by no means surprising, Olson supposes Google’s decision to publicize the breach was unusual. Typically, companies are wary of publicizing such leaks for fear that perceptions of insecurity could negatively affect their business. The explanation may lie in the fact that Google executives, who had continually met resistance from the Chinese government regarding censorship since the company had entered the Chinese market in 2006, finally decided enough was enough.
Google first learned of the attack from Chinese human rights activists in the US who had reported that their Gmail accounts had been accessed by unknown users. As details of Operation Aurora, as it was called, surfaced, it became clear that the attack was highly tailored and complex. The cyber spies exploited a flaw in Internet Explorer 6.0 to gain access to targeted computers. Once the vulnerability was identified, the hackers determined which officials at various companies had access to sensitive information. Emails that, once opened, installed malate on the target computers were then sent from servers in Taiwan to the chosen company officials. The hackers from then on had unfettered access to the officials’ computers and could steal any information they deemed valuable. Google was not the only US firm targeted by the Aurora cyber spies. No less than 34 companies, to include Yahoo, Symantec, Adobe, North run Grumman, and Dow Chemical, were victimized. The Washington Times reported, “Each of the companies was targeted differently, using software developed from the attackers’ knowledge of the individual networks and information storage devices, operating systems, the location of targeted data, how it was protected, and who had access to it.” According to federal cybersecurity experts, attacks of Aurora’s precision and sophistication could be achieved only with substantial the government’s support.
Perhaps the most egregious of all the attacks on US computer systems became public in June 2015, when the Office of Personnel Management (OPM) announced that its database had been breached by unknown persons. The personnel records of 21.5 million US government employees, past and present–including Social Security numbers, biographical information, and the results of security background investigations–were stolen. The information, in Olson’s informed view, would be a gold mine for any intelligence service seeking to spot, access, and develop US government employees for future recruitment. The US Intelligence Community placed blame for the attack squarely on China. Beijing denied any official responsibility for the breach and, in fact, announced in December 2015 that it had arrested a small group of nongovernmental hackers for having committed the crime. No information was provided on the hackers’ identities, place of deployment, or sentencing. Skeptics suspected a convenient cover-up to ease tensions with the US before a scheduled visit of People’s Republic of China President Xi Jinping. Olson s that the only Chinese entity, state sponsored or otherwise, that he could think of that would have a motive for stealing all the OPM data is the MSS. The administration of US President Barack Obama signed a bilateral agreement in September 2015 pledging that neither side would use cyber attacks to steal intellectual property for commercial purposes. According to Olson, a US cybersecurity company documented a Chinese cyberattack on a US company the day after the agreement was signed. In the three weeks that followed, there were at least seven more attacks from China against US high-tech companies.

The current director of the Russian Federation’s Sluzhba Vneshney Razvedki (Foreign Intelligence Service) or SVR, Sergey Naryshkin (above). Second place on Olson’s list of counterintelligence threats to the US goes to the Russian Federation Following the Soviet Union’s collapse, the monolithic Komitet Gosudarstvennoy Bezopasnosti (the Committee for State Security) or KGB. was divided into two new agencies, the Federal’naya Sluzhba Bezopasnosti Rossiyskoy Federatsi (Russian Federation Federal Security Service) or FSB and Sluzhba Vneshney Razvedki (Foreign Intelligence Service) or SVR. Despite the democratic posturing and economic liberalization of the early years, in the end, not to much changed about Russian activity in the US. Many of the KGB’s old and young guard stayed on and simply moved into new offices in Yasenevo for the SVR or the Lubyanka for the FSB.
Russia
Second place on Olson’s list of counterintelligence threats to the US goes to the Russian Federation (Russia). Despite the democratic posturing and economic liberalization of the early years following the collapse of the Soviet Union, Russian security services did not change much. Intelligence was reorganized in Russia in 1991. The monolithic Soviet Komitet Gosudarstvennoy Bezopasnosti (the Committee for State Security) or KGB. was divided into two new agencies, the Federal’naya Sluzhba Bezopasnosti Rossiyskoy Federatsi (Russian Federation Federal Security Service) or FSB and Sluzhba Vneshney Razvedki (Foreign Intelligence Service) or SVR. Unlike the former satellite countries of the Eastern Bloc (e.g., Poland, Bulgaria, Czechoslovakia, East Germany, Romania, Hungary, Latvia, Lithuania, and Estonia), where intelligence services of the new democratic regimes purged old Communist apparatchiks, many of the KGB’s old and young guard stayed on and simply moved into new offices in Yasenevo for the SVR or the Lubyanka for the FSB. The Russians did not consider it professionally disqualifying for someone to have served previously in the repressive and undemocratic KGB. When Olson mentions that organization, it must be made clear that he viewed it as “a ruthless and vicious organization that oppressed its own people, crushed religion, sent political dissidents to gulags or psychiatric hospitals, and killed its enemies.” Olson describes the FSB as being responsible for Internal security in Russia, specifically counterintelligence, counterterrorism, domestic unrest, state crimes, and border security. Meanwhile, the SVR is responsible for external intelligence collection and covert action. With this structure Russia has aligned itself more closely to the US and United Kingdom models , in that the FSB is the rough equivalent of the FBI or the Security Service (popularly referred to as MI5) and the SVR corresponds to the CIA or the Special Intelligence Service, popularly known as MI6. (An explanation of the United Kingdom’s nomenclature of MI5 and MI6 is provided in some detail in greatcharlie’s December 11, 2020 post.) Russian military intelligence is the responsibility of the Glavnoye Razvedyvatel’noye Upravleniye Generalnovo Shtaba (Main Intelligence Directorate of the General Staff-Military Intelligence) or GRU which has operated under that name since World War II.
Olson says that there was real optimism, even a belief in some quarters, that the US Intelligence Community could forge a new relationship with the Russian intelligence services on the basis of trust and cooperation, particularly in areas of common concern, transnational interests. They included counterterrorism, narcotics, and organized crime. Olson said that some of the early talks between representatives of the two services were so encouraging that “the US side decided it did not want to jeopardize this potential intelligence détente by getting caught in any kind of provocative spying against our new ‘friends.’” The problem with that line of thinking was illustrated by Olson when pointed to the episode of former KGB archivist Vasil Mitrokhin. Mitrokhin provided MI6 with a gold mine of documentary intelligence on Russian espionage information from the revolution to the 1980s. However, Mitrokhin had initially attempted to provide the information to the CIA, but Olson explained he was rebuffed based on the rationale that the CIA did not want to antagonise the SVR given its aims of establishing a cooperative relationship with that Russian intelligence service.
Then what Olson describes as an avalanche of bad news came when it was discovered that both the SVR and the GRU intelligence operations against US personnel and installations worldwide had never ceased. They were in fact being conducted aggressively. Olson then points to the cases of CIA officers Aldrich Ames, Edward Lee Howard, Harold James Nicholson, FBI special agents Earl Edwin Pitts and Robert Philip Hanssen, and the US Army’s George Trofimoff.
Another Russia concern to which Olson draws the reader’s attention was the case of a group of illegals–described by Olson as professional intelligence officers living in the US under false identities–intercepted by the FBI in 2010. The case was made very public and news stories on it garnered considerable public interest, with focus placed on a divorce, Anna Chapman, who held dual Russian and United Kingdom citizenship. Olson remarks on the politics of the illegals detainment, trial, and exchange. Olson also gives attention to Russian information warfare, which he explains supplements their human intelligence efforts.
Cyber spying is widely used by Russia to interfere in the politics of other foundries, to manipulate their populations, to spread disinformation, to conduct unconventional warfare, and to collect intelligence. The Russian objective is to harass, to discredit, to disrupt, to deceive, and to spy on rival states. The last ten years have seen not only a dramatic increase in the frequency of Russian cyber activity, but also, what Olson alarmingly characterizes as a quantum leap in the brazeness, sophistication, and destructiveness of the attacks.
Olson reports that the FSB has taken the lead in launching denial-of-service attacks on foreign governments and sponsoring anonymous “web brigades” that bombard political blogs and other forums with disinformation and pro-Russian propaganda. The GRU’s cyber capabilities are primarily directed at supporting military interventions, but the GRU is suspected of also having carried out cyber attacks on non-military objectives, such as the German Bundesamt and French television station. The lines of responsibility between the FSB and GRU are blurry and overlap, leading to a possible duplication of cyber efforts. The SVR uses cyber operations to support human intelligence operations. Although it is not as directly involved in cyber operations as the FSB and GRU are, it plays a planning role in overall cyber strategy.
According to Olson, Russian cyberspying first surfaced on the world stage in a big way in Estonia in 2007. Russian-Estonian relations fell to a new low over the removal of a Russian war memorial. At the height of the controversy, Estonia was hit by a massive denial-of-service attack on government offices, political parties, banks, and media outlets. In 2008, as a prelude to the Russian armed forces invasion of the Republic of Georgia, the voluntary was victimised by well-orchestrated cyber attacks creating disarray. Internet services were rerouted and blocked, websites were defaced with pro-Russian propaganda, and news agencies websites were attacked, and in some cases brought down. The Russian annexation of Crimea in 2014 was followed by waves of sophisticated cyber attacks against Ukraine’s central government in Kiev. Separate attacks on energy suppliers, the power grid, the financial sector in Ukraine, as well as the Ministry of Defense in years since.
Olson asserts that unlike Chinese espionage, which he characterized as being based on China’s cold, objective attitude toward the US, an impersonal self-interest, Russian spying is predicated on a certain animus toward the US. Olson concludes that Russian Federation President Vladimir Putin “does not like us,” and says his grudge is personal. Olson believes that in sheltering Edward Snowden, who he describes as a “contemptible US turncoat,” Putin is showing his disdain for the US.
Olson informs that when the US Intelligence Community is interviewing applicants for employment today, it sometimes refers to the “Big Five” foreign languages that are in highest demand: Chinese, Arabic, Farsi, Korean, and Russian. The Russian language is still on the list for good reasons, not the least of which is that the SVR and the GRU are all over us. Olson believes that Russia will remain a major counterintelligence concern for the US for the foreseeable future. He concludes that the US would be naive in the extreme to believe that it could ever expect good faith from Putin.

Ana Montes (above) was a Defense Intelligence Agency analyst arrested in 2001 on charges of committing espionage on behalf of Cuba. According to Olson, the Cuban DGI was the most effective intelligence service the US counterintelligence faced. A noteworthy aspect of Cuban intelligence activity in the US is the quality of the tradecraft. In the case of Montes, for 16 years she passed the DGI everything she could get her hands on related to US counterintelligence efforts against Cuba. It was no small feat for the Cubans to run her case and others as long as they did and in hostile territory under the noses of US security and counterintelligence officials without getting caught. (Olson gives the Montes case substantial treatment in Chapter Eight.)
Cuba
Olson’s review of the Cuban threat was perhaps the best written of the three assessments. Olson declares that the Cuban Intelligence service may be the most effective service that US counterintelligence services face. The Cuban Intelligence Directorate, formerly known as General Intelligence Directorate or DGI was established by the First Secretary of the Communist Party of Cuba, one time Cuban Prime Minister, then Cuban President, Fidel Castro, in 1961 to preserve the Revolution; to collect intelligence on Cubans enemies, both foreign and domestic; and, to carry out covert action operations as directed. Castro was aware as early as 1961 that President Kennedy and his brother Robert Kennedy, the US Attorney General, were trying to have him assassinated through a variety of CIA plots that never came anywhere near fruition. The DGI reportedly became Castro’s tool of choice to carry out his vendetta against the CIA and the US.
Olson states the Cuban DGI cannot compete with the Chinese or the Russians in terms of overall damage to US national security, but that is primarily a function of its smaller size, narrower objectives, and limited resources. However, perhaps it should have been added, as Olson is surely aware, under furtive cooperative arrangements, foreign intelligence services, not knowing the true nefarious nature of a case, are often asked or position themselves, to support the intelligence efforts of other countries when there is a common interest or considerable benefits of all kinds. Reportedly, friendly foreign intelligence services are often asked to engage in surveillance activities and initiate clandestine contacts with innocent US citizens outside and inside the US. Many foreign intelligence services of other countries, particularly medium to small sized organizations actually love being brought into US intelligence operations of any kind. It gives them the opportunity to have a place at the table with the US, there will usually be important lessons learned, supposedly good relationships with US counterparts will be enhanced or created, and most of all, there will be financial benefits courtesy of the US taxpayer.
In their recruitment operations against the US, Olson reveals that the Cubans, much as the Chinese, often benefited from non-monetary inducements, ideological in the case of the Cubans, ethnic in the case of the Chinese. That sort of recruitment is often facilitated by the fact that many of the US citizens who worked for the DGI and the MSS essentially volunteered their services. Another noteworthy aspect of Cuban intelligence activity in the US that Olson points to is the quality of the tradecraft. The longevity of an espionage operation is largely a result not only of the skill of the handling officer but also the techniques and equipment used to run the operation securely.
Olson reveals that in 1998, the FBI broke up a large Cuban espionage operation in South Florida called the Wasp Network (Red Avispa). This network consisted of fourteen or more Cuban spies who had the mission of penetrating anti-Castro organizations in Florida. Evidence against some of the members was too thin for prosecution, but five ringleaders stood trial and we’re convicted of espionage and other crimes. One of the Cuban-American groups, the Wasp Network, infiltrated was an organization named Brothers to the Rescue. Brothers to the rescue flew aircraft in and around Cuban airspace to assist people fleeing in boats and to drop anti-Communist propaganda leaflets. The organization was clearly a thorn in Castro’s side. As the story goes, a member of the Wasp Network found out the flight plan of Brothers to the Rescue flight to Cuba in February 1996. Cuban fighter aircraft shot down the plane in international airspace, and all four Cuban-American on board were killed. (It stands to reason that the Soviet Union, which in its day essentially armed the Cuban military and security forces, would have provided Cuba with more than a rudimentary capability to monitor nonmilitary flights from the US that did not use electronic countermeasures as well as the weapons systems to shoot down from the ground and fighter-jets that could scramble and intercept Brothers to the Rescue missions. Perhaps there was a greater reason to shoot down the 1996 flight, due to someone in particular being on board or to demonstrate Cubans capability to some operatives or informants that supported the collection of the flight plan, that led to what occurred.)
While Olson gives the case of Ana Montes greater treatment in Chapter 8 “Counterintelligence Case Studies,” notes in this chapter that due was a Defense Intelligence Agency analyst arrested in 2001 on charges of committing espionage on behalf of Cuba for at least 16 years. During that period Montes passed the DGI everything she could get her hands on related to US counterintelligence efforts against Cuba. Olson writes that the tradecraft the Cubans used in handling Montes was fantastic, a credit to the art of espionage. Olson comments that it was no small feat for the Cubans to run cases as long as they did and in hostile territory under the noses of US security and counterintelligence officials without getting caught. Montes was sentenced to 25 years in prison.
Interestingly, Olson notes here that the CIA could penetrate the KGB and sometimes count on it to make tradecraft mistakes, but it was not so fortunate when dealing with the the DGI. Perhaps Olson was a bit exuberant about presenting the DGI as a formidable foe or maybe there was some simple oversight, but the notion that the Cuban intelligence was somehow less able to make mistakes somewhat contradicts what was one of the more remarkable aspects of the Montes case as recounted in the text. As Olson describes in Chapter 8, Montes was coached by DGI on tradecraft to include erasing everything incriminating from her hard drive. He notes that Montes either did not follow instructions or they did not work because the FBI recovered a treasure trove of espionage traffic on her Toshiba laptop.
Olson goes on to discuss the case of a retired State Department official, Kendall Myers, and his wife, Gwendolyn Myers, who were arrested on charges of having been DGI agents for almost 30 years. Myers joined the US Foreign Service with a top secret clearance in 1977. Later he was given even higher clearances when he was assigned to the highly sensitive Bureau of Intelligence and Research at the State Department. Myers sympathised with the Cuban Revolution and believed that the US was subjecting Cuban government and people to unfair treatment. His response, probably beginning in 1979, was to spy for Cuba. With help from his wife, Gwendolyn, he engaged in a full-fledged espionage relationship with the DGI. Until Myers’ retirement in 2007, he passed top-secret documents and other classified material to the DGI in a sophisticated system of dead drops and brush passes. During their trial, it became known that the Myers had received personal congratulations from Fidel Castro. The damage they did to US national security was incalculable.
As for the CIA’s recruitment of DGI officers, it was more likely that there would be a walk-in, attempting to escape from problems of their own making with the DGI. The case Olson points to is that of Florentino Aspalllaga Lombard. Referred to by Olson as Aspillaga, he was the highest ranking defector from DGI that the US ever had. Olson was directly involved in his case. In 1987, while Olson was posted to the US Embassy in Vienna, he was summoned to his office by an agreed parole indicating that there was a walk-in. That walk-in was Aspillaga, and he was accompanied by a teenaged girl who was his mistress and the daughter of an official of the Cuban Embassy in Prague. Aspillaga, had left his wife and three children and was on the run, hoping to find a new life as a couple in the US. Aspillaga offered their services to the CIA as barter.
In what Olson called a sensational revelation, Aspillaga told the CIA that former CIA officer Philip Agee had cooperated with the DGI and had been paid close to $1 million. Agee’s role as a DGI agent was later confirmed by former KGB officer Oleg Kalugin, citing his memoir, Spymaster: My 32 Years in Intelligence and Espionage against the West (Smith Gryphon, 1994) as his source. Kalugin said Agee had walked into the KGB in 1973, had been turned away as a suspected provocation, and then had gone to the Cubans. Agee, a graduate of the University of Notre Dame, joined the CIA in 1957. He served in a series of undercover assignments in Latin America in the 1960s, supposedly becoming more and more disillusioned by what he considered CIA support of right wing dictatorships. While assigned to Mexico City in 1968, Agee resigned from the agency, moved to Europe, and began his new career of neutralizing the CIA. In 1975, he published a book, Inside the Company: CIA Diary, a detailed description of his career and exposé of CIA activities in Latin America. Most damaging of all, he included the names of 250 CIA undercover officers and foreign agents (operatives and informants). thereby disrupting CIA officers’ clandestine careers and subjecting them to considerable personal risk. The foreign agents he identified were exposed to the even worse fate of possible imprisonment or execution. The CIA chief of station in Athens in December 1975, shortly after he was outed by Agee. Agee’s guilt has never been proven conclusively, but few CIA officers believe that the timing of Welch’s killing was a coincidence.
Olson states that Agee’s US passport was revoked in 1979, but he still traveled widely, mostly in Europe, for the next several years using passports provided by the leftist governments of Grenada and Nicaragua. In subsequent books and magazine articles, Agee continued his denunciations of the CIA and the US government and disclosed the identities of an additional one thousand CIA officers and agents. Olson states here that it was clear at that point that he was not operating on his own but was getting help from a foreign intelligence service. Olson does not explain or support this fact with any data. Hopefully, he is not theorizing on a hunch but is rather presenting an inference that he can support. Whenever one theorizes in such a way without fact, one makes a capital mistake. Olson goes on to explain, unfortunately, under US law at the time, the unauthorized disclosure of the names of undercover US personnel was not a crime, so Agee could not be indicted and extradited to the US. Additionally, he remarks that Agee was operating on behalf of the DGI could not be denied after 1989. Then by Olson to state Agee’s involvement with the KGB was a near certainty because of the close relationship that existed between the DGI and the KGB. To support this, Olson points to a statement by Kalugin in Spymaster that he read reporting from Agee that the DGI passed to the KGB. Olson claims it is inconceivable to me that the KGB would let its client service run a source of this magnitude without inserting itself into the operation.
Yet, despite what Olson inferred, the data may suggest otherwise. By Olson’s own admission, the KGB rejected Agee for recruitment in 1973. Senior executives and managers at Moscow headquarters would need to reverse a decision. They may not have been that flexible. The DGI apparently rejected the KGB’s original evaluation of Agree. That seemed even more interesting to consider. Olson then reveals that in 1989, Agee played a key role in a DGI operation against the CIA. He posed as a CIA official from the inspector general’s office in a fiendishly clever recruitment operation against a young CIA officer stationed in Mexico City. Mexico City was once Agee’s beat for the CIA, at least until 1968. Still, Agree was completely unrecognizable to US Embassy security as well as Mexican authorities. Mexico City was also being watched closely as it had a well-known role as launch pad for Soviet and Eastern Bloc operations against the US, particularly California, Nevada New Mexico, Arizona, and Texas. Reportedly, Agee contacted the CIA officer and told her that he was conducting a sensitive investigation of alleged wrongdoing by the CIA in Mexico City, possibly involving senior management. He asked for her help in carrying out a discreet investigation that would not alert the targets. Agee ordered her on behalf of the inspector general not to discuss his approach with anyone. He managed to elicit significant information from the young officer.
As far as recruiting DGI officers, Olson did not provide any information on such operations being successful. Rather, from another revelation by the DGI walk-in, Aspillaga, it was discovered that all 38 of the Cubans the CIA thought it had recruited over the previous 26 years were double agents, controlled and running against the US by the DGI. This was a devastating indictment of CIA counterintelligence, one of the worst and most embarrassing compromises we ever had. Olson laments, “The DGI beat us–and beat us soundly.” According to Olson, the CIA’s damage assessment was long and painful. The intelligence that the CIA disseminated from the bogus agents had to be recalled since it was all DGI-concocted disinformation. The CIA’s tradecraft handling the controlled agents had been completely exposed to the DGI, which later ridiculed the CIA in a TV special for the agency’s alleged amateurishness and sloppiness. The CIA lost all the clandestine equipment it had provided to the Cuban assets, including a then state-of-the-art burst satellite communications system. Olson also considers that the cash that the CIA paid to the Cuban doubles in salaries and bonuses, ended up in the DGI’s coffers.
In a rare expression of analysis in this segment of To Catch a Spy, Olson looks at how the CIA could have walked so far into the DGI’s counterintelligence trap. Olson pointed to the following factors. First, he explains that the CIA was so eager to have sources in Cuba that looked the other way when none of the agents produced any real intelligence of value. Many of the double agents reported that they were “on the verge” of meaningful access, but they never quite got there. The CIA settled for chicken feed. Second, intelligence officers always want their recruitment service to turn out well. They do not want to admit that they have been duped by a double agent. In their desire to succeed against the Cuban target, the CIA’s handling officers rationalised away the questionable reporting, anomalous behaviors, and ambiguous polygraph results of their agents. Third, the quality of counterintelligence at the CIA during much of this period was undermined by the poor leadership of James Jesus Angleton, whose obsessive focus on the KGB and overall paranoia blinded him to other counterintelligence threats. Fourth, the CIA grossly underestimated the skill and sophistication of the DGI.
A few low key remedies may have mitigated or capitalized on the possibility the CIA’s double agents were still working for the other side. Perhaps one might be added to what Olson offered by noting that there should have been an established practice of constantly interviewing agents, even in debriefings to collect intelligence and discuss requirements. It would put extra pressure on those controlling them to try to alleviate what may be concerns of fidelity, and either improve what is being offered to placate or across to board changes in methods of communicating indicating some central control exists for all that are active. The CIA could have suddenly asked that all active agents from DGI produce information away from the area of an existing expressed interest and measure the timing it took each to deliver the information, the sources they used to gather the information, and interview the agents to discover what background they agents would use to assure the quality of the source and identify similarities that sounded more like a scripted story. It may not immediately smoke out and identify who were the double agents and who was true, and none were true in the Cuban case, but it might have gone a long way to encourage the CIA to consider the possibility of deception and that their double agents were fake.
Perhaps to go a step further, the CIA needed to ensure that those handling agents were not biased pro or con toward the double agents, and were open minded to consider the possibility of deception in a way that would not color interactions with them. (That would recognizably have been less possible in a less socially conscious agency of the past.) In some cases, CIA officers perhaps could have very steadily, yet gradually sought to convince their double agents that they, themselves, might be open to recruitment by DGI. The task then would be to wait and see if there would be an effort by their double agents to manipulate and push them to some DGI operative or officer to size them up for recruitment or whether a DGI officer would simply step up out of nowhere to size them up for recruitment. That surely establishes the double agent’s loyalties, but may lead to the opening of an entirely new door to penetrate the DGI’s operations in the US. Potential must be seen in all directions when sources are limited as in the Cuban case then, and the China case now.
These three chapters are among those in which complaints arose over Olson’s decision not provide enough answers to, and copious insights on, the many “whys” of adversarial foreign intelligence activities, left gaps in understanding the reasoning behind them. For example, there is no discussion of how within not only the respective bureaucratic system, but also under the political systems in which those adversarial intelligence services work, unwavering parameters for operating are set. From that one might better conceptualize how ongoing and future operations of those services could be sorted and categorized from apples to nuts. From that analysis, antecedents in US counterintelligence would be better enabled to understand and effectively fashion operations to defeat in going and future efforts by those adversaries.
However, it must be reminded that Olson, as he reveals in his introductory Acknowledgements, submitted To Catch a Spy to his former employer, the CIA. The Publications Review Board surely stopped anything from going into the text before it got too close to classified information. That preliminary screening might explain why some reviewers commented that the book reads at points much as a heavily redacted document.
In Olson’s case, his former employer’s solemn warning of secrecy was increased with regard to the knowledge he retained as any information that would provide some nuance on how the US detects and catches spies would be of the utmost interest and importance to the foreign intelligence services of adversaries as well as allies. Facts are somewhat easy to judge as they may be classified and one can reasonably determine what their value might be to an adversary. Hypotheses and arguments are a bit more challenging to judge for security reasons as certain facts, even if left out, can be viewed as being confirmed by them, seeing that those facts might alone be the sole solid basis upon which a particular inference could logically be made. Surely those hypotheses and arguments might be helpful to an adversary in developing any Red Team exercise. To that extent, security considerations may be the main reason why Olson avoids drawing too many inferences and presenting too many theories in the text. Olson would hardly be the type to neglect any precaution. However, his former employer likely preferred to be safe, not sorry.
All of that being stated, greatcharlie would to some degree concur that the portraits Olson paints of the Russian, Cuban and Chinese intelligence services are somewhat two dimensional. Drawing a perspective from military science, recall that an opposing force should not be viewed as some inert, non thinking body, waiting to be acted upon. There is an aphorism trained into the minds of mid-level Army officers at the Command and General Staff College that “the enemy has a say.” It falls in line with a teaching of the 19th Century Prussian military thinker, Carl Von Clausewitz, that: one’s opponent (in just about any endeavor, not just war) is “a living force” and military plans must factor in that what is being planned is “the collision of two living forces.” One must have respect for what an opponent thinks to be successful. More specifically, one must objectively gauge what the opponent thinks and what the opponent can do. What greatcharlie would have preferred to read would be an exposition of his presence of mind, inspiring insights, written in a clear and elegant style that would make Marcus Aurelius proud and would fit in beautifully in Meditations or Epictetus’ Discourses. One might have expected that along with an insistence the novice US counterintelligence officers become and remain dedicated to improving themselves. Such will always be a worthy theme and purpose of an offering from the expert veteran to the junior worm.
Olson’s Ten Commandments
Of interest to greatcharlie was Olson’s discussion of his Ten Commandments of Counterintelligence. Those commandments ostensibly reflect the general sensibilities, perspectives, strategies, and tactics of US counterintelligence services. In his conclusion of this chapter, Olson states: “These are my Ten Commandments of Counterintelligence. Other CI professionals will have their own priorities and exhortations and will disagree with mine. That is as it should be, because as a country and as a counterintelligence community, we need a vigorous debate on the future direction of US CI. Not everyone will agree with the specifics or the priorities. What we should all agree on, is that strong CI must be a national priority. He then proceeds to set out what he views as the Ten Commandments of Counterintelligence. Previously published in 2001 as an article in the CIA’s periodical, Studies in Intelligence, these commandments include such concepts as playing offense rather than defense, owning the street, paying attention to analysis, and not staying in the profession too long.
The 20th century French Algerian philosopher, author, and journalist. Albert Camus, in his Notebooks, 1935-1942 stated: “You cannot create experience. You must undergo it.” Olson is not attempting to promote such through his efforts at this point in To Catch A Spy. Indeed, at this point in the text, Olson presents future and novice counterintelligence officers a leg up by providing a heads up on what they might expect. Understood is his desire to prevail upon the novice to heed certain realities and precepts that would not be included in their initial training. Two issues are in play in Olson’s discussion of his commandments, competence and commitment. Looking at each issue covered by a commandment, he seeks to instruct and counsel in advance, but he wants officers to focus on being competent in their work and understand the commitment that counterintelligence work requires. This is all very handsome of Olson. Clearly, a fair and decent man of honorable intent. His scruple does him great honor.
A concern for greatcharlie however is that at no point in his discussion of his Ten Commandments does Olson offer a thought about innocent citizens caught in a US counterintelligence web. With so many investigations that can get underway when so many foreign intelligence services are working hard in the US, as indicated in Olson’s first three chapters concerning People’s Republic of China, Russian Federation, and Cuban operations, innocent private US citizens can get caught in the mix erroneously with calamitous results for the citizen through no fault of their own. In a Constitutional republic, that is a grave error and greatcharlie believes such matters if utmost importance must be broached with those moving along in the counterintelligence track. Nil magnum nisi bonum. (Nothing is great unless it is good.)
Unpacking everything about Olson’s commandments here would require dedicating too much of this review’s analysis to it and shift its focus. It may be enough to say that greatcharlie found some disconcerting and a few exceedingly problematic. The information provided by Olson in his discussion of them sets off a kind of warning light that flashes “Beware” to free citizens of a Constitutional Republic. His commandments of particular note are: The Tenth Commandment; the Ninth Commandment; and, the Eighth Commandment. By focusing on these three of his ten commandments, the opportunity to understand and taste what creates concern is provided. They are presented in reverse order here to better illustrate the cascading development of Olson’s perspectives within them on some key matters.

Captured FBI turncoat Robert Hanssen (above). Olson states from the outset that it is a profession in which officers will go for months and even years without perceptible progress or accomplishments. Olson explains: “A typical CI [counterintelligence] investigation starts with a kernel, a fragment, or a hunch that is hard to grab onto but that demands attention. He further explains: “There is no statute of limitations on espionage, and we should not create one with our own inaction. Traitors should know that they will never be safe and will never have a peaceful night’s sleep.” Still, he calls attention to a misdirected investigation tied to the counterintelligence case against special agent Robert Hanssen that uncovered him as a Soviet spy, He notes that investigation went on longer than it should have because time and energy wasted on chasing an innocent man. Olson does not comment on how much harm and torment, the innocent man suffered as a result of the wrongful investigation of him as a spy. No matter how singular one’s percipience, until one personally suffers an injustice of a wrongful counterintelligence investigation, one cannot really fathom how damaging, even life changing, it can be.
In his “Tenth Commandment,” Olson explains that counterintelligence requires tenacity and persistence, and that is a slow, plodding process that rarely rewards its practitioners with instant gratification. He advises that one chooses to pursue a career in counterintelligence, one should know from the outset that it is a profession in which officers will go for months and even years without perceptible progress or accomplishments. Olson explains: “A typical CI [counterintelligence] investigation starts with a kernel, a fragment, or a hunch that is hard to grab onto but that demands attention. He lists what types of information qualifies as such. He then explains how counterintelligence investigations usually start with little and face an uphill fight.” He further explains: “There is no statute of limitations on espionage, and we should not create one with our own inaction. Traitors should know that they will never be safe and will never have a peaceful night’s sleep.” As for a rationale behind what could very well turn out to be a Quixotic search for evidence that is not there against a target who may very well be innocent, Olson states: “If we keep a CI [counterintelligence] investigation alive and stay on it, the next defector, the next penetration, the next tip, the next piece of CI analysis, the next wiretap, the next surveillance report, the next communications intercept, i.e. the next four will break it for us. If US counterintelligence ever had a mascot, it should be the pit bull.” Readers must be reminded that this would all be done at taxpayers’ expense.
Hypotheses and conclusions should be predicated and driven by hard evidence, not appearances, presumptions, and surmisal, supporting a preconception of guilt. A type hubris ensnares and overwhelms the investigator much as the fisherman in Ernest Hemingway’s The Old Man and the Sea (Charles Scribner’s Sons, 1952). When moving into the realm of conjecture, anything becomes a possibility. In that realm, everyone is entitled to a hypothesis. Each one, within reason, is likely equally correct or incorrect. Less elevated reasons may have a familiar ring to some involved in counterintelligence: “Somethings got to be there because I can tell!”; “I know he is bad because I feel it!” To get an investigation of a subject where a counterintelligence officer wants it to be, the focus can shift from The actual matter at hand to a secondary search through extraneous matters–sifting through dust figuratively–for “good” information that is just not there. That will lead those officers to settle for something close enough to the truth that should never pass muster among somber and astute supervisors, but it could for others.
Preconception is abhorrent to the cold and precise mind. The pure objective truth must be the focus. It may be harder to find, but it is the true pathway to success in an investigation. True evidence must be there. Must be predicated only on a reasonable standard, logic, and the law. A thorough review of superiors, auditors is needed not simply to curtail but to provide another voice, extra eyes on the matter. Sometimes an ally looking into a matter to see and call attention to issue an investigator too close to it may overlook. The situation worsens when bent information, which can always be found or sought, may be used to support very wrong ideas. Intuition and hunches can be colored, or better yet poisoned, by extraneous matters. Before placing the full force of the powers of secret intelligence services upon a citizen to impinge on his or her rights, something more than a hunch or feeling must guide the pursuit. Tools available to US counterintelligence services for surveillance and investigation have become far more powerful and intrusive than the US Congress and even the federal courts could have imagined or conceptualized while promulgating laws on their use. A tragic consequence of a lack of strong supervision is that the punishing weight of government power that can potentially be placed on the subject with those tools, who may actually be innocent, can be harmful, damaging, and destructive. There must be constraint on the use of powerful, highly intrusive government tools to pursue a subject of an investigation. Knowing when to say when, especially since a human life is in the balance, is the mark of a true professional in any field. There must be an inner-voice or one from a supervisor that warns that an investigation could be going down a totally wrong path. In his Discourse on the Method of Rightly Conducting One’s Reason and of Seeking Truth in the Sciences, 17th century French-born philosopher, mathematician, and scientist, Rene Descartes, explained: “The first precept was never to accept a thing as true until I knew it as such without a single doubt.”
Conducting a heavy-handed counterintelligence investigation of an individual not yet found guilty of anything in a court of law can ruin that individual’s life permanently. The damage counterintelligence services can do to a subject’s psyche is well understood to be grave and considerable. Use of surveillance methods of all kinds, invasion of privacy, discussing the subject with family, friends, work colleagues in a manner that skirts defamation or fully crosses the line, using informants among neighbors work colleagues, friends, as well as family, eliminating the possibility of normal human contact, and more, all ensures nothing normal with be left in the subject’s personal life. The soul and the spirit of the subject is typically seared. Reversing the damage, is extraordinarily difficult, if not impossible. The psychological capsule in which strong willed subjects will seek refuge in order to hold on to the remainder of themselves, to survive, is never easy to break open in an effort to find them. However, there seems to be little sensitivity with US counterintelligence services to the harm done to the innocent from wrongful investigations. Olson actually calls attention to a misdirected investigation tied to the FBI’s famed counterintelligence case against Special Agent Robert Hanssen that uncovered him as a Russian [Soviet] spy, He notes that investigation went on longer than it should have and essentially glosses over the fact that time and energy was wasted chasing an innocent man. Nowhere does he mention how much harm, how much torment, the innocent man suffered as a result of the wrongful investigation of him as a Soviet spy. That speaks volumes. No matter how singular one’s percipience, until one personally suffers an injustice of a wrongful counterintelligence investigation, one cannot really fathom how damaging, even life changing, it can be.
Habet aliquid ex iniquo omne magnum exemplum, quod contra singulos, utilitate publica rependitur. (Every great example of punishment has in it some tincture of injustice, but the wrong to individuals is compensated by the promotion of the public good.) The failure to practice what the US Constitution preaches regarding life and liberty and law is reflective of an individual engaged in an investigation going off the rails. However, that individual’s frustration or any other internal conflicts, must not allow for devaluation of the system, and a devolution that can comfortably lead US counterintelligence services to regularly mimic the tactics, techniques, procedures, and methods of an authoritarian security service as stated earlier. The way of life in the US, the country’s values and interests, are not being defended. Indeed, something very different would be happening. The US and liberal democracies must be different. Government actions are founded under laws that amplify morals, Judeo-Christian values of its founders. If all that Olson declares as essential to a counterintelligence investigation is permissible as a practice in a free society, a liberal democracy as US, it stands to reason the possibilities and capabilities make the potential for harsh behavior in search of enemies far worse in China’s authoritarian–arguably totalitarian–regime.
Olson begins the discussion of his Ninth Commandment in his purest tone with the statement: “Counterintelligence is a hazardous profession. There should be warning signs on the walls of CI [counterintelligence] offices around the intelligence community: ‘A steady diet of CI can be dangerous for your health.'” Following some interesting anecdotes about officers and senior executives in CI who seemed to lose themselves in the work, Olson explains: “I do not believe anyone should make an entire, uninterrupted career out of CI. All of us who have worked in counterintelligence have seen the old CI hand who has gone spooky. It is hard to immerse oneself daily in the arcane and twisted world of CI without falling prey to creeping paranoia, distortion, warping, and overzealousness in one’s thinking. It is precisely these traits that led to some of the worst CI disasters in our history.” In addition, Olson notes that following a lunch with a CIA colleague who had worked for a time in counterintelligence said: “Jim, after doing CI for two years I felt the occupational madness closing in on me. I had to move on and do something else before I lost my bearings.”
Olson argues that differences in sensibilities and approaches among CIA case officers, FBI special agents, and military intelligence officers are great/disparate enough that when working together on a case, insular thinking is mitigated. Thereby, he suggests officers from different US counterintelligence services should rotate among their offices to exploit the benefits cooperation can bring. However, despite some differences among the officers in some lines of thinking, they are all from the same national security bureaucracy and their collective thinking would more likely tend to manifest greater commonalities, more similarities, than differences, having been trained and functioning in the same system. That may not be as discernible from the inside. To be frank, but not impolitic, so far, in the case of Chinese intelligence efforts in the US, no marked positive impact has been evinced from the aggregated efforts of the services.
With all of the pearl clutching being done among senior executives in the US counterintelligence service about Chinese intelligence successes in their country, taking the approaches presented in those “Ten Commandments,” out of sort of desperation, overlooking, or turning a blind eye, to aberrant situations, prolonged investigations, “tabs” being kept on former operatives and informers for no logical reason or constructive reason, obsessive surveillance, use of dirty tricks, services ou les activités pour traquer ou nuire à autrui. They can often end up becoming huge expenditures with no constructive results, only destructive ones. Being able to claim that one is on the trail of some questionable former ally might achieve some meretricious effect in a meeting to review cases–the errant officer may want to create the appearance of being a sleuthhound with a never surrender attitude–but such efforts will typically accomplish nothing to protect the US from its adversaries or enhance the country’s national security. The dreadful consequences for those incorrectly targeted, would be, as has been, the recipe for disaster. US counterintelligence, not a foreign adversary, has, and will always be, harming innocent, private US citizens in those cases.
Supervisors and those managers of US counterintelligence services close enough to the rank and file and their operations in the field must judge the actions of officers against US citizens based on the seriousness and dignity of the claim. If there are strong concerns, there may be other avenues along which the potential problem could be managed. Suffice it to say that an investigation of a private US citizen using tools designed for trained foreign intelligence officers and networks have no good reason to be used on a citizen in a Constitutional republic. That will always be a dangerous and destructive undertaking in terms of the well-being of the US citizen. (One wonders how inspired those US counterintelligence officers who are often anxious to spend so much time, energy, and especially money on chasing tenuous leads and entertaining the slender appearance of a private US citizen’s guilt or complicity, if money was short and was being appropriated from their personal accounts. Perhaps none!)
As for another pitfall reality that taking such a harsh, seemingly ego driven approach to counterintelligence in the present day, it could lead to self-inflicted walk down a garden path and into the hands of US adversaries. Newly minted MSS counterintelligence officers in “on the job training,” which is how they do it, may very well be actually working in the field, using decoys under their trainers direction as a type of net practice for gaining and retaining the attention of foreign counterintelligence services and luring their resources, energies, and time, into endless, fruitless pursuits. The indications and implications of what is provided in Olson’s, albeit well-meaning, “Ten Commandments” are that US counterintelligence services would be susceptible to such a ploy. MSS counterintelligence could surely offer just the right amount of chicken feed here and there to support a misguided belief that the perfect “kernel” of information will be found to make a case. Such an effort could effectively distract, divert, and disrupt elements of US counterintelligence officers from engaging in more worthier pursuits against what may very well be in many cases, potentially vulnerable networks and operations of Chinese intelligence services in the US. (Interestingly, in public announcements by the US Department of Justice of a Chinese intelligence and counterintelligence operation being cracked or disrupted, there is never mention of any apparent plot to lure US intelligence services into a trap. Perchance, since Chinese intelligence services have been so successful in the US, there is no reason, no impetus to play such games. In the eyes of senior executives and managers of the MSS and senior commanders of the PLA, US intelligence and counterintelligence services may no longer be worth the candle.)
Taking draconian steps against a US citizen for allegedly, presumptively, or imaginably being tied to a foreign intelligence service when that is in reality not the case could very well compound an already difficult situation with regard to recruiting adversarial intelligence officers, operatives, and informants. The rationale for making that representation is if a US counterintelligence service accused a US citizen of providing some assistance to a specific foreign intelligence service, and the assertion is false, no group other than that adversarial service would know for a fact that the accusation is false. Even more, observing the US counterintelligence service initiate some severe, intrusive investigation of the citizen, ostensibly to better understand US practices. Surely such behavior, such practices by some US counterintelligence services would create a decidedly negative impression of the US among members of an adversarial foreign intelligence service.
“Once upon a time” there was a near universal notion of the US being “the good guy,” known for its largesse. That reputation has become a bit tarnished over time quite possibly as result of such aggressive actions by a US counterintelligence service against their own innocent citizens. If a foreign intelligence officer, operative, or informant would ever consider what would befall him or her if they left their service and country and turned to the US, the individual would need to ask himself or herself: “If they treat their own people that way, how would they treat an adversary.” Through Olson’s compendium of US activities by adversaries and his case studies, one could infer that since the end of the Cold War, foreign intelligence officers were more likely to turn to the US only if they ran afoul of their own organizations after making some egregious, irreconcilable misstep on a professional or personal level, either by their own volition or through entrapment. Such individuals would prefer to save their skins in any way possible with an intelligence service willing to accept and protect them, rather than face their superiors. One might speculate on how many occasions the choice was made by a foreign intelligence officer to turn to another country’s intelligence service such as the United Kingdom’s Security Service or Secret Intelligence Service rather than walk-in into a US Embassy or Consulate to prostrate himself or herself. Perchance some venturous officer in a US counterintelligence service might want to apply a bit of the preceding logic to the Chinese intelligence conundrum.
Perhaps one should also consider that adversarial foreign intelligence officers may chalk up actions of US counterintelligence officers performed against them, such as monitoring an opponent’s telephone and electronic communications, surveilling their movements, or striking up clandestine conversations, as a matter of them simply doing their jobs. Such thinking would form the basis of a tacit, or even an explicitly agreed upon, modus vivendi. However, it is another thing altogether for US counterintelligence officers to use “dirty tricks” against adversarial foreign intelligence officers or their families and make their circumstances unviable in the US while deployed under official cover. Boiling it all down, there must be hope, even assurance, that there will be an intelligent connection for the one who defects not a bullying connection with a US counterintelligence officer. The one coming over of course wants help in doing so, needs help in betraying his own. Those individuals are the proverbial “bigger fish to fry.”

Infamous former chief of CIA Counterintelligence, James Jesus Angleton (above). Olson initially mentions Angleton in Chapter 3 when he discusses how his obsessive focus on the KGB and overall paranoia blinded him to other counterintelligence threats. In his Ten Commandments, Olson makes note of the counterintelligence failures and abuses of Angleton, the FBI’s J. Edgar Hoover, and their subordinates, reminding of the obsessive harassment of Martin Luther King in the 1950s and 1960s, Olson states “the practice of counterintelligence–whether in intelligence, law enforcement, the military, or corporate security–is highly susceptible to overzealousness. To take the discussion of such problems further, he notes: “Counterintelligence officers must be wary of what I call the ‘self-righteousness trap,’ that is, our objective cannot be so righteous and our motives so pure that we can justify inappropriate and illegal methods.”
In his explanation of his Eighth Commandment, Olson begins by reminding readers of what was mentioned in his “Second Commandment” that “some people in the intelligence business and elsewhere in the US government do not like counterintelligence officers.” He makes note of the counterintelligence failures and abuses of the CIA’s James Jesus Angleton, the FBI’s J. Edgar Hoover, and their subordinates and reminding of the obsessive harassment of Martin Luther King in the 1950s and 1960s, and then states “the practice of counterintelligence–whether in intelligence, law enforcement, the military, or corporate security–is highly susceptible to overzealousness. To take the discussion of such problems further, he notes: “Counterintelligence officers must be wary of what I call the ‘self-righteousness trap,’ that is, our objective cannot be so righteous and our motives so pure that we can justify inappropriate and illegal methods.”
To explain the reaction within the national security bureaucracy and among government contractors to counterintelligence officers, Olson simply states that case officers, special agents, commanders, and other managers have a natural tendency to resist counterintelligence scrutiny. As a rationale for that, Olson asserts that they believe that they are practicing good counterintelligence themselves and do not welcome being second guessed or told how to run their operations by so-called counterintelligence specialists who are not directly involved in the operation and not in the chain of command. He acknowledges that defense contractors and other civilian bureaucrats running sensitive US government programs have too often minimized counterintelligence threats and resisted professional counterintelligence intervention. As a rationale for that perspective, Olson says they view counterintelligence officers as only stirring up problems and overreacting to them. They perceive counterintelligence officers “success” in preventing problems as being invisible and their damage assessments after compromises as usually being overblown.
In the face of such resistance, Olson proffers that counterintelligence officers must act heroically, stating: “A counterintelligence officer worthy of the name must be prepared to speak unpopular truth to power, even at the potential cost of poor performance appraisals or missed promotions. It is not an exaggeration to say that a good CI [counterintelligence] officer must be a nag–and as we all know, imperious managers do not like persistent and vocal dissent.” Intriguingly, In this discussion, Olson leaves the reader with the impression that all counterintelligence investigators are first class individuals, straight as a dart. Across all of the US counterintelligence services, a majority probably are. However, in his Ninth Commandment, he clearly indicates personal problems among them are known to arise as a consequence of the work, to repeat included: creeping paranoia, distortion, warping, and overzealousness in one’s thinking. To reiterate what he writes even in this “Eighth Commandment,” Olson mentions the “self-righteousness trap” and acknowledges: “the practice of counterintelligence–whether in intelligence, law enforcement, the military, or corporate security–is highly susceptible to overzealousness.” When Olson recalls from his experience how senior executives and managers in CIA shied away from acceptance of counterintelligence officers in their divisions and shops, surely he is fully aware that they could only express that choice through tidy, plausible and professional statements such as those. He also had to know that they were very likely aware of the same problems Olson, himself, indicated could exist among some counterintelligence officers. Not presuming or expecting to learn of a connection between stories of aberrant behavior by counterintelligence officers and concerns that raises among managers of departments and units, the issue may escape the impressions of many readers. To that extent, Olson, perhaps unconsciously, does say enough to invite such concerns to be among reader’s impressions either.
Iniqua raro maximis virtutibus fortuna parcit; nemo se tuto diu periculis offerre tam crebris potest; quem saepe transit casus, aliquando invenit. (Unrighteous fortune seldom spares the highest worth; no one with safety can long front so frequent perils. Whom calamity oft passes by she finds at last.) With such problems among counterintelligence officers in mind, as a “good shepherd,” the goal of any attentive and prudent manager would be to keep a potential source of undue trouble from his flock. Letting counterintelligence officers in has really become a high stakes gamble. The slightest suggestion that a manager might refuse to receive a fellow officer due to unsubstantiated concerns that he or she may be potentially psychologically unfit to carry out his or her duties appropriately or concerns that he is she may be of questionable judgment–again, based on Olson’s own statement about problems that can arise among counterintelligence officers, it could always be a possibility–could lead to sanction from the top. Olson surely must have understood was likely a tad sympathetic to such underlying sensibilities among managers within the CIA and the other national security bureaucracies about counterintelligence. If there is so much concern within the federal bureaucracies over US counterintelligence, certainly the unsuspecting, unprotected citizen has far more to fear from it. Gnawing again at the subject of the “potential” abuse of power by US counterintelligence officers, as long as there is the actuation and potential for transgressions of innocent citizens’ rights exists, there may be less to fear about China expropriation of the US role as the dominant power in the world and its usurping of citizens rights, primarily through infiltration of elite circles and election interference, than the prospect of being torn to pieces as a result of the acts, benign or malicious, of a few trusted men and women in the intelligence services and law enforcement.
Very easily the innocent, with no connection to the hideous business of a spy ring, can be caught in the same net as the guilty. It is among the innocent, carrying on by appearance in the same manner as them, that the foreign intelligence officer, operative, and informant conceals himself or herself. Suppositions based on assumptions can result in an officer initiating a case green-lit with all the necessary approvals from the top. Sentimentality to the concept of beginning, middle, and end should not compel the endless pursuit of one who may upon informed consideration may equally be found innocent. Wrongs already done cannot be righted, but an energetic effort should be made to prevent future wrongs of the same kind. Pause for thought!
Once the track to find an individual is guilty has been taken, no one among the officers in the shop will aim to prove the individual’s innocence. The individual’s innocence becomes by the by. In these matters, perception errantly means more than reality. That imbalance in thought unfortunately has likely served to allow all formulations based on available evidence, easing in tragic results. Surely adversarial foreign intelligence services would prefer US counterintelligence service would become immersed in an investigation of an innocent party than put their time and energy on any actual part of their networks. As discussed in somewhat greater detail in the August 31, 2020 greatcharlie post entitled, “China’s Ministry of State Security: What Is This Hammer the Communist Party of China’s Arm Swings in Its Campaign Against the US? (Part 2),” it cannot be overemphasized that misidentifying an innocent citizen as an agent of an adversarial foreign power engaged in espionage or some other act on its behalf by initiating an investigation against the individual, to include securing warrants for the most intrusive and egregious acts contrary to his or her First and Fourth Amendment Rights under the Constitution is a tragedy of unimaginable proportion and can have enormous consequences upon the life of the one mistakenly, even wrongfully targeted.
In a December 1999 federal indictment, Wen Ho Lee was charged in 59 counts concerning the tampering, altering, concealing, and removing restricted data, the receipt of restricted data, the unlawful gathering of national defense information, and the unlawful retention of national defense information. As the investigation into his alleged espionage began, Lee was fired from his job at Los Alamos by the University of California, Los Angeles (UCLA) on March 8, 1990, under pressure from the US Department of Energy, which oversees the laboratory. The news media was informed of his dismissal by an unknown source and the stories were widely reported. While his alleged espionage was being reported, the FBI had determined that Lee could not plausibly have been the source of information on the W88 passed to China. The normative hope, yet perhaps a bit of an optimistic one given the players involved, would be that once exculpatory information is discovered that could prove one’s innocence, a FBI investigation would have been halted. However, the FBI moved forward with its investigation of Lee. Although the original espionage charge was dropped by the FBI, Lee was still charged with the improper handling of restricted data. In September 2000, Lee pled guilty to one count as a part of a plea bargain arrangement. The other 58 counts were dropped. Later, Lee filed a lawsuit against the US government and five news organizations–the Washington Post, New York Times, Los Angeles Times, ABC NEWS, and the Associated Press–for leaking information that violated his privacy.
Lee and his supporters have argued that he was unfairly singled out for investigation because he was Chinese-American. Wen Ho Lee was not the enemy but has been called a victim of the blind, unfettered power of a few men with authority. That bit of humanity that should exist in each human heart was in such insufficient quantity in the counterintelligence special agents handling his case. In his book Securing the State, David Omand, former United Kingdom intelligence and security coordinator, wrote security intelligence operations—such as counterterrorism and counterintelligence—require cooperation between security officials and civilian populations among whom threats wish to hide. In the case of Chinese intelligence, this includes ethnic Chinese émigré communities, which, at least in the US, are now suspicious of the FBI. The botched investigation of Wen Ho Lee, in Ormand’s view, appeared to be politically (or racially) motivated witch hints rather than the serious security investigations they were. To Chinese-Americans, these suspicions and resulting investigations are the natural result of an unwillingness to analyze Chinese intelligence more rigorously on the basis of evidence.
Intelligence enthusiasts may find it interestingly that in a September 25, 1977 New York Times interview, John le Carré, the renowned espionage novelist of the United Kingdom who served in both MI5 and MI6, just after publishing The Honourable Schoolboy (Alfred L. Knopf, 1977), was asked about a view implied in his earlier works that no society was worth defending by the kind of methods he had set out to expose in his books. In reply, the author stated in part: “What I suppose I would wish to see is the cleaning of our own stable and the proper organization, as I understand it, and the sanitization, of the things that we stand for. I hope by that means and by those examples perhaps to avoid what I regard as so wrong with the Soviet Union.”
Double-Agent Operations and Managing Double-Agent Operations
Olson follows his commandments with a chapter on preventing counterintelligence incursions through the development of better workplace security. Improvement may be achieved, he explains, by following his “Three Principles of Workplace Counterintelligence”—careful hiring, proper supervision, and responsible promotions. Afterward, comes the chapters of To Catch a Spy that greatcharlie appreciated the most were “Chapter Six: Double-Agent Operations” and “Chapter Seven: Managing Double-Agent Operations.” In these two chapters, Olson finally presents a classical series of demonstrations. Indeed, in both chapters, Olson provides nothing less than a mini manual for precisely what the titles indicate. Readers are favored with many of the logical principles that Olson would practice and expound during training while working in CIA counterintelligence. He provides a list of benefits US counterintelligence seeks to gain from a double agent operations: spreading disinformation; determining the other side’s modus operandi; identifying hostile intelligence officers; learning the opposition’s intelligence collection requirements; acquiring positive intelligence; tying up the opposition’s operations; taking the oppositions money; discrediting the opposition; testing other countries; and, pitching the hostile case officer. Nihil est aliud magnum quam multa minuta. (Every great thing is composed of many things that are small.)
The tactics, techniques, procedures, and methods of US counterintelligence are laid out. Some portions are couched in anecdotes illustrating practices used in the past. Each to an extent is a display of the imagination possessed and creative ways in which double-agents were dangled to garner interest from the adversarial intelligence service, the transmission of chicken feed, ostensibly useful yet actually useless information, for the adversary to grab, and management of nuanced communications between the double agent and his handler. Olson does not indicate whether any among the practices discussed was used by him to achieve some crowning glory of his career. Again, for readers such as greatcharlie, what was presented in this chapter was meat and drink. None of the precepts included were beyond the understanding and the abilities of most readers who would be interested in the book. He tells it all in an apposite way.
Case Studies
In “Chapter Eight: Counterintelligence Case Studies,” Olson goes into some greater detail on the principles and methods of counterintelligence. Olson carefully avoids offering what may seem to some as a mere series of tales. However, it seems that Olson’s relaxed writing style, present throughout the text in fact, may distracted some previous reviewers’ attention away from the instructive nature of the discussion. In the 12 case studies he presents, Olson also illustrates the tradecraft of counterintelligence, and where counterintelligence breaks down or succeeds. He presents, to the extent that he could, how US counterintelligence officers became fully engaged on each matter. To some degree, Olson also looks at the other side of things and discusses why people spy against their country.
Each case study is followed by a “lessons learned” section. Lessons learned are the pertinent qualities and deficiencies that Olson ascribes to each case pertinent to the ongoing work of US counterintelligence services. The lessons learned are given greater value for Olson selects only what he deems most pertinent from what he witnessed, experienced, and endured as is not presumed. Again, nothing presented in To Catch a Spy is considered in the abstract. Some might observe that absent again is the severe reasoning from cause to effect that helps to solve the case. Instead, he highlights a few points of interest in each and considerable focus is put into placing color and life into his discussion of them. Two good examples of his case studies are those concerning Ana Montes and Richard Miller.

Scott Carmichael (above) was the senior security and counterintelligence investigator for the Defense Intelligence Agency and the lead agent on the successful spy hunt that led to Ana Montes. Concerning the Montes case, Olson does not deny the fact that the DGI had done the thing very completely. Of the lessons learned, the three most important to Olson appeared to be that the DIA was wrong not to require polygraph of its new employees. He applauded the DIA for having in place a policy that encouraged employees to come forward with any workplace counterintelligence concerns that they had. The report of Montes’ suspicious behavior in 1996 turned out to be inconclusive but still served the purpose of putting her on the counterintelligence radar of DIA investigator Scott Carmichael, who he heaps praise upon. Olson also notes that penetration is the best counterintelligence. Without the FBI source to raise the alarm and put Carmichael back on the scent, Olson says Montes might have stayed in place.
Ana Montes
Concerning the case of Ana Montes, which Olson touched upon in his country report on Cuba in Chapter 3, he leaves no doubt that it was a very complicated and abstruse case. He does not deny the fact that the DGI had done the thing very completely. Olson referred to Ana Montes as a classic spy. Montes worked for Cuban intelligence for sixteen years. She was indeed the embodiment of an ideological belief concerning US policy in Latin America and most of all, a pro-Cuba sentiment, as she carried out her espionage duties for the DGI diligently and effectively. Before the smash of her unmasking, Montes was believed to be a thoroughly trustworthy officer. When colleagues learned of Montes’ betrayal, it was a crushing blow to them.
Olson reports that Montes’ views against the US role in world affairs were hardened while she studied abroad in Spain as a student of the University of Virginia. Nevertheless she would eventually find employment in the US Department of Justice and receive a top secret security clearance required for her position. The espionage problem started outright when Montes, already a federal employee, began attending night courses at the Johns Hopkins School of Advanced International Studies in Washington. Montes, likely spotted by someone working for Cuban intelligence once she was heard voicing her negative views toward US policy in Central America during the administration of US President Ronald Reagan. The Cubans, appreciative of her enthusiasm, Olson believes, Cuban intelligence insisted that she leave her job at the US Department of Justice and move to a national security organization. She secured a job with DIA. Starting as an analyst on El Salvador and Nicaragua, Montes rose to become the senior DIA analyst on Cuba.
As for her espionage work for the Cubans, Montes would memorize contents of documents she saw, summarized it at home, and encrypt the material on diskettes. She received instructions from Havana by shortwave radio broadcasts, which she deciphered on her Toshiba laptop using a special program the Cubans provided her. She would contact her handler by calling from a public phone booth and sending a coded message via her pager. She would have dinner with her handler once or twice a month with her Cuban handler in a Washington restaurant to provide him with the diskettes. Montes was lavished with praise but never accepted payment.
In 1996, an alert DIA employee, practicing good workplace counterintelligence, reported his concerns about Montes to DIA counterintelligence officer Scott Carmichael. The employee noted that Montes appeared sympathetic to the Cuban cause, and inappropriately aggressive in seeking expanded access to sensitive intelligence on Cuba. Carmichael interviewed Montes and eventually dropped the matter. However, as Olson explained, he filed away his suspicions of her for future action. In 2000, Carmichael became aware that the FBI was looking for a Cuban mole inside the US intelligence community. Only soupçons were known about the identity of the spy, except that he or she was using a Toshiba laptop to communicate with Cuban intelligence. Carmichael immediately thought of Montes, but he had little evidence to support his suspicions against her that he had great difficulty in convincing the FBI to open an investigation.
Carmichael remained persistent in pushing the FBI to open an investigation (never give up), egged on by further aberrant pro-Cuban attitudes displayed by Montes, and his efforts finally succeeded. In May 2001, the FBI threw its notorious full court press at Montes, starting with extensive physical surveillance. It did not take long for the FBI to conclude that she was involved in illegal activity. First, she was obvious and amateurish in her surveillance detection routes, often entering a store by one door and quickly leaving by another. Second, she made a succession of one minute phone calls from public phone booths, even though she owned a car and carried a cellphone. Montes’ behavior was suspicious enough to the FBI that it was able to obtain a warrant for surreptitious entry of her apartment on May 28, 2001. She was away on a weekend trip with her boyfriend. The FBI knew that this entry would be particularly dicey if Montes was a Cuban trained spy, she could have trapped her apartment to determine the intrusion. There was, however, no evidence of trapping and the entry was successful. The FBI found a shortwave radio of the type used by spies to listen to encrypted broadcasts and a telltale Toshiba laptop. On the hard drive, which the FBI drained, were multiple messages from the Cubans to Montes on her intelligence reporting, giving her additional tasking requirements, and coaching her on her tradecraft. Olson says he is certain that the FBI computer experts chuckled when they read the instructions from the Cubans to Montes on how to erase everything incriminating from her hard drive. He further comments that she either did not follow the instructions or they did not work because the FBI recovered a treasure trove of espionage traffic. One message thanked Montes for identifying an undercover US intelligence officer who was being assigned to Cuba. It was later determined that she gave the Cubans the names of other US intelligence personnel in Cuba. She blew their cover and sabotaged their mission.
As the remainder of the story goes, the FBI continued its surveillance of Montes for another four months in hope of identifying her Cuban handler or handlers. That effort was not successful, but the FBI was able to search her purse when she was out of her DIA office to attend a meeting. Inside her purse the FBI found more incriminating material, including the page rhinestone number she used to send short corded messages to the Cubans. Olson said the fear was that if Montes detected the surveillance, she would flee. When Montes was about to gain access to US war planning for Afghanistan in the aftermath of September 11, 2001, the FBI and DIA decided that they could wait no longer. Montes was arrested at DIA Headquarters on September 21, 2001. She pleaded guilty on October 16, 2002 and was sentenced to 25 years in prison.
Of the lessons learned, the three most important to Olson appeared to be that the DIA was wrong not to require polygraphs of its new employees. He applauded the DIA for having in place a policy that encouraged employees to come forward with any workplace counterintelligence concerns that they had. The report of Montes’ suspicious behavior in 1996 turned out to be inconclusive but still served the purpose of putting her on Carmichael’s counterintelligence radar. Olson also notes that penetration is the best counterintelligence. Without the FBI source to raise the alarm and to put Carmichael back on the scent, Montes might still be in place. DGI’s activities in the US were really a mystery. Olson did well in presenting readers with a sense of the elusive nature of DGI operatives.
As it turned out, the case did not reach its optimal potential for counterintelligence officers engaged in the investigation were unable to use available information to track down and capture Montes’ handlers or any other elements of the Cuban espionage network of which she was a part. In his investigation, the DIA counterintelligence officer, Carmichael, was able to observe, reflect, and intuit connections based.on facts not conjure a false reality based merely on appearances. Again, it is always a capital mistake to theorize in advance of hard facts. Nevertheless, it is a common errant practice. With hard facts, one is better enabled to grasp the truth.
With regard to Olson’s suggestion that the FBI computer experts likely chuckled over the failure of Montes to eliminate incriminating evidence from her Toshiba laptop, a concern is raised. Perhaps some in US counterintelligence services may feel greatcharlie is making the whole matter seem more urgent and important than it really is, but the proper comportment, displayed and demanded by supervisors and line managers, would instead have been to remain collected and aplomb with noses to the grindstone in the squad, knowing that an unexpected opportunity to exploit a failing on the part of the adversary has shown itself. It may signal that other missteps by the adversary may be present that will allow counterintelligence officers to net an even greater quarry of foreign intelligence prey. Recognizably, stresses can cause attention to shift. (Take charge of your emotions!) However, there is the need to concentrate solely on performing the duty of the moment as best as possible. Once the case is resolved, there would be time then to reflect on its many aspects. The reputation of US counterintelligence services will not suffer shipwreck over this particular matter. Olson surely did not view at all out of order as he freely revealed it in the text.
When Montes’ handlers and the managers of her undiscovered network evaded capture, they took with them all their lessons learned. (Recall her activities were not a small matter in the DGI as the informative walk-in Olson dealt with in Prague, Lombard, was read-in on her fruitful work while he was posted in Vienna.) One could have no doubt that meant it would certainly be decidedly more difficult, after the DGI presumably made necessary corrections, to uncover their activities of officers, operatives, and informants in their networks on later occasions. Surely, they would be back. (Rather than display any good humor about the matter, it should have been handled from start to finish with solemnity, especially given the indications and implications of the case.)

KGB operative Svetlana Ogorodnikov (above). As described by Olson, Richard Miller was a disaster as a counterintelligence officer, and an FBI special agent in general. However, that aspect is key to understanding the lessons the case presents not only to senior executives and managers of US counterintelligence services, but among the rank and file of each organization. Working out of the Los Angeles FBI Office, Miller was tasked to monitor the Russisn émigré community in Los Angeles. In May 1984, a well-known member of the Russisn émigré community called Miller suggesting that they meet. It turned out the caller, Svetlana Ogorodnikov, was a KGB operative dispatched in 1973 to infiltrate the Russian emigre community in Los Angeles. She got her hooks into Miller. Miller, figuratively tied to a tether right in front of the KGB, was exactly the type of FBI Special Sgent that an adversarial foreign intelligence officer would look for.
Richard Miller
As described by Olson, Richard Miller was a disaster as a counterintelligence officer, and an FBI special agent in general. However, that aspect is key to understanding the lessons the case presents not only to senior executives and managers of US counterintelligence services, but among the rank and file of each organization. Miller was a door left open that an adversarial foreign intelligence service, in this instance the KGB, was happy to walk through, and one could expect in similar circumstances that will almost always be the case.
Olson notes that Miller was hired by the FBI in 1964. After having spent time in a number of FBI field offices, Miller landed in the Los Angeles FBI Field Office where he should have found peace. However, as Olson explains, Miller, as a result of his own incompetence did not find a happy home in that office. Olson leaves no doubt that Miller was a disaster as an FBI special agent. He was a laughingstock at the office. His FBI colleagues scratched their heads in disbelief that he had been hired in the first place. In the buttoned down world of the FBI, he was totally out of place. He was poorly dressed and noticeably careless with his grooming. His weight and physical fitness did not meet the FBI’s rigorous standards. At 5’9″ tall and weighing as much as 250 pounds, he never came close to matching the stereotypical profile of the trim and athletic FBI special agent.
To make matters worse, Miller was hopelessly incompetent. Olson says Miller begged his FBI colleagues to give him assets because he was incapable of developing any on his own. At various times, he lost his FBI credentials, gun, and office keys. His performance reviews were consistently bad, but somehow his career chugged on. In Olson’s own words, Miller was part of the FBI culture that did not turn on its own, even at the cost of carrying dead weight. With eight children, on a special agents salary, Miller was always on the lookout for extra income. Reportedly, he stole money from his uncle in a far fetched invention scam. He pocketed money that was supposed to pay assets. He ran license plates for a private investigator. He sold Amway products out of the trunk of his office FBI vehicle. He even bought an avocado farm to profit from but it went under. Miller would eventually be excommunicated from the Church of Latter Day Saints for adultery and divorced while serving in Los Angeles.
Miller’s initial work in the Los Angeles FBI Field Office was in criminal work but he was unsuccessful at that. He was transferred to goreign counterintelligence where it was ostensibly though he would receive vlossr supervision and mentorship from the Gordian counterintelligence chief. Olson notes that additionally, foreign counterintelligence was considered a dumping ground for under performing employees Counterintelligence was not highly regarded and the best people stayed away.
In foreign counterintelligence, Miller was given the job to monitor the large Russian émigré community in Los Angeles. To do that job he was expected to mingle with the émigrés and develop contacts inside that community who could keep him informed of any indications of Russian espionage. It was not hard to imagine how Miller was perceived by the Russians with whom he came in vintage. There is no indication that Miller did anything significant during that period. His career and personal life was still spiraling downward. He would later tell estimators he sometimes took three hour lunches at a 7-Eleven store reading comic books and eating shoplifter candy bars. Viewing Miller’s behavior was becoming increasingly erratic he was counseled by his supervisor and sent in for a mental health assessment. Although found emotionally unstable, and subsequently suspended for being overweight, Miller was krot pn at foreign counterintelligence. He was allowed to hang on until he reached retirement age of 50.
In May 1984, one of the well-known members of the Russisn émigré community called Miller suggesting that they meet. The caller,, Svetlana Ogorodnikov, immigrated from the Soviet Union in 1973 with her husband Nikolai. She worked as a low level source for the FBI at one point but dropped out. Her husband worked as a meatpacker. It turned out that Svetlana was a KGB operative, dispatched in 1973 to infiltrate the Russisn emigre community in Los Angeles, and if possible, assess and develop US citizens for recruitment. She was known to make trips to the Soviet Consulate in San Francisco which the FBI would later assess were occasions when she met her KGB contact.
Olson assesses due to the timing of Ogorodnikov’s call, she likely was aware from her contact in the community that Miller was in trouble at the FBI and his personal life had become a shambles. Olson also supposes that the KGB green-lit her call after they were satisfied with an assessment of him. After traveling to the Soviet Union, where Olson believes she met with the KGB to discuss Miller, Ogorodnikov returned to the US and continued contact with him in August. She promised him cash for secrets and Miller agreed. He supplied her with secret FBI documents to prove his bona fides. Miller then met with a KGB officer. Olson explained that the KGB was not immediately satisfied with Miller. He gave his FBI credentials to Ogorodnikov who presented them to heathen contacts in the San Francisco Consulate. The KGB wanted Miller to travel to Vienna with Ogorodnikov to meet with more intelligence officials. However, the FBI never allowed that to happen; other special agents became aware of Miller’s unauthorized relationship with Ogorodnikov. Miller was placed under surveillance by use of wiretaps, bugs, and operatives on the street.
Olson assumes Miller detected the surveillance. On September 27, 1984, he tried to convince the FBI that he was engaged in his own effort to catch Ogorodnikov. However, while being polygraphed he admitted to his malign activities. He gave Ogorodnikov a secret document. He then started keeping several other documents in his home and was prepared to present them to the KGB. Miller and the Ogorodnikovs plead guilty to conspiracy to commit espionage on October 3, 1984.
In his lessons learned, Olson focuses on the decision of Miller’s FBI superiors to keep Miller in place. He does not fault the other special agents in the office for not reporting him because Miller’s situation was well-known in the office. Olson, to some extent in the role of apologist, offers reasons for such behavior among Miller’s colleagues. Misfortune can easily come at the hands of an evil influence such as alcohol. Miller had a weakening nature to which his supervisors should have responded. Perhaps they figured they had to stretch a point in favor of a man who served for so long. However, by keeping Miller on the job, his supervisors and managers, surely inadvertently compounded the problem. They went too far to screen his many disqualifications from their own superiors, presumably to allow him to reach retirement. Miller seemingly marked his zero point when he was approached by the KGB. It stands to reason that an astute counterintelligence officer may often discover weaknesses and blind spots in himself or herself. An effort to correct the deficiency would then be in order. However, Miller was different. By all appearances, he was spent, no longer qualified to serve, but he was kept on.
On reflection, the matter seems almost ridiculous. Miller was exactly the type of FBI special agent that an adversarial foreign intelligence officer would look for. He was not a dangle, nor was he really on the prowl. He was simply a door left open to the achievement of some success by the KGB, figuratively tied to a tether right in front of them. Perhaps at the time their agents presented him as a prospect, in Moscow, they could hardly believe their luck. The opportunity was there, and the KGB operatives among the émigrés supplied the audacity to take advantage of it.
Through his own insufficient and perhaps sympathetic investigation, he discovered no one and nothing significant among the émigrés. Anyone getting involved with an émigré community as part of a counterintelligence investigation must gird one’s loins, for with some certitude adversarial foreign intelligence services will very.likely be quietly operating among both suspicious and unwitting émigrés. The powers of such officers or operatives may seem far superior to opportunities that may present themselves, but they are deployed among the émigrés nonetheless. The erstwhile KGB and DGI, and current SVR and MSS, each organized special departments for such work. Indeed, an emigre community can very often be a milieu for spies. Perhaps Miller’s FBI superiors thought he would unlikely find trouble in the Russian émigré community, and Miller had effectively been sent to some empty corner of the room. However, they confused the unlikely with the impossible. By their experience and instincts, his supervisors should have been against Miller’s conclusions. Nevertheless, they were satisfied with his totally erroneous conclusions.
Given his history of behavior, it is very likely that during his contacts with the Russian émigré community, Miller betrayed himself with an indiscretion or two. Whatever it may have been, it was clearly significant enough to cause KGB operatives–who he was unable to detect as tasked under his original counterintelligence mission–to seize upon him as their prey. The case highlights the KGB’s–and presumably now the SVR’s–ability to figuratively pick up the scent of blood much as a shark, and recognizing there can be a good soup in an old chicken. Even more relevant to the discussion in proceeding parts of this review, it illustrated the real possibility for errant officers ro exist in plainview within the rank and file of other hardworking, diligent counterintelligence officers. Such license could only lead to some great evil. The KGB Rezident at the time would have been derelict of his duties if he had not recruited Miller, a wayward FBI special agent, who due to that errant choice made by his superiors, was placed in counterintelligence. And, given his deficiencies, it would have been a serious blunder for the KGB not to exploit all possibilities with Miller to the maximum extent.
It is likely that any other KGB comrades, who may have concealed themselves in the same roost among émigrés in which Svetlana and her confederate had set themselves and had perhaps taken to their heels once they learned those two and Miller were captured, is unclear. Further, it is unclear whether any concern was raised that there was any increased concern that other KGB operatives had continued to secrete themselves among Soviet emigre groups throughout the US. For whatever reason, Olson does not go into such details on what would have been legitimate counterintelligence concerns.
No one should imagine that this review, or any other for that matter, fully covers what Olson offers in To Catch a Spy. It presents the essence of the book, but there is so much more to discover. As humbly noted when the review started off, there nothing that greatcharlie appreciates more about such a book than its ability to stir the readers curiosity, inquiry into the author’s judgments, greater consideration of their own views on the matter, and elicits fresh insights based on what is presented. That is exactly the type of book that To Catch a Spy is. One can ascribe these positive aspects to it and many others. What one finds in To Catch a Spy is of the considerable quality. The book remains steady from beginning to end. Readers are also enabled to see the world through the lens of a man with years of experience in the world and a thorough understanding of humanity.
Whenever greatcharlie feels so enthusiastic over a book, the concern is raised that its review may be written off as an oleagic encomium. However, that is not the case, and readers will understand once they sit with the book. Despite concerns about what To Catch a Spy is missing, it would be worth reading to see what appears to lie at the base of such positions and take one’s own deeper look into Olson’s discussion. Having engaged in that process itself, greatcharlie found it thoroughly edifying. It is assured that after the first reading To Catch a Spy in this manner, one would most likely go back to the book and engage in that stimulating process again and again.
With To Catch a Spy, Olson confirmed his reputation as an excellent writer in the genre of intelligence studies. The book will also likely serve for years as an inspiration to future author’s on the subject of counterintelligence. As aforementioned, the book will surely be consulted as a reference for intelligence professionals and prompting new ideas and insights among intelligence professionals, law enforcement officers, other professional investigators, and scholars. The rudiments of counterintelligence tactics, techniques and procedures, and methods offered by Olson, to some degree, may also serve as a source for guidance Indeed, much of what is within can aptly serve as a foundation upon which they will construct new approaches.
Further, both by what he includes and ironically by what he omits in the text, became the supplier/purveyor of a foundation upon which an honest discussion can be had among people inside and outside of counterintelligence services in free societies–well-known constitutional republics and liberal democracies in particular–can look at themselves and their organization’s work relative to the rights and interests of the citizens of the respective countries they defend. It is a conversation to which greatcharlie believes To Catch a Spy can lend support. It is a conversation in current times, especially within the US, that many citizens greatly desire to have. Without hesitation, greatcharlie recommends To Catch a Spy to its readers.
By Mark Edmond Clark