Senator Frank Church holding a poison dart gun developed by the US Intelligence Community (left) and Senator John Tower observing (right) at the Church Committee’s first open session on September 17, 1975. In the wake of Watergate, Church was tasked with investigating abuses of power by the US Intelligence Community. Rather than noting mere oversteps by the Intelligence Community, Church and his Congressional Committee put forth dark truths about its work that they uncovered. Indeed, Church exposed a myriad of clandestine and covert plots orchestrated by the Central Intelligence Agency (CIA), the National Security Agency (NSA) and the Federal Bureau of Investigation (FBI) as well as other federal organizations. In many cases, singular actions were taken by the Intelligence Community actually amounted to criminal violations of federal law. This essay is not a book review. Instead, it is a literary insight essay providing meditations of Risen’s The Last Honest Man. In this essay, greatcharlie’s insights are delimited to a discussion of occasional rogue behavior, abuses of law, by members of the US Intelligence Community. The book is remarkably suggestive with respect to contemporary times. Such an edict surely requires examination. In this essay, readers may come upon aspects of issues or view new angles of the discussion they may not have not recognized or perhaps would not have considered after reading the book.
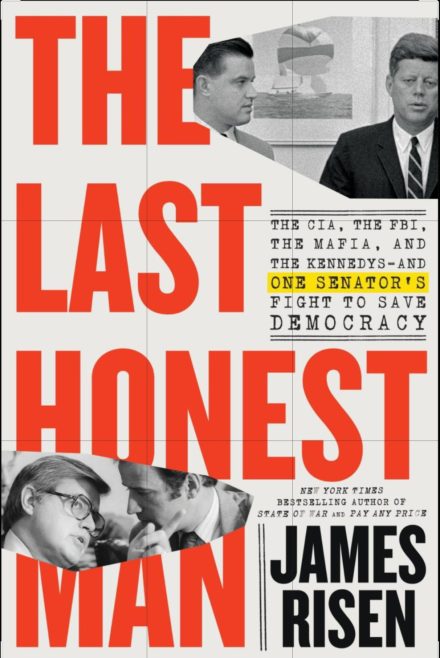
James Risen’s The Last Honest Man: The CIA, the FBI, the NSA, the Mafia, and the Kennedys–and One Senator’s Fight to Save Democracy (Little, Brown and Company, 2023), [ISBN-13 9780316565134] tells the story of how Frank Church, at the the time Senator of Idaho for almost two decades, attempted to reign in US Intelligence Community activities in 1975 after years of no Congressional oversight. Risen draws upon hundreds of interviews, thousands of pages of recently declassified documents, and reams of unpublished letters, notes, and memoirs, some of which remain sensitive today. The story as told in the 480 page tome is true to reality.
As a Senator, Church promoted, advocated, and vigorously defended the US Constitution. He was guided by US values and supported its interests. Church’s beliefs would compel him to lead congressional opposition to the Vietnam War and had become a scathing, radical critic of what he saw as US imperialism around the world. Yet, Risen suggests the “rebellious” Church was politically ambitious, and sough acceptance from the foreign and national security policy establishment of which he was very skeptical. He was also interested in running for president. The author indicates that Church was not devoid of faults. In the wake of Watergate Church was tasked with investigating abuses of power by the US intelligence community. Rather than noting mere oversteps by the Intelligence Community, Church and his Committee put forth dark truths about its work that they uncovered. Indeed, Church exposed a myriad of clandestine and covert plots orchestrated by the Central Intelligence Agency (CIA), the National Security Agency (NSA) and the Federal Bureau of Investigation (FBI) as well as other federal organizations. In many cases, singular actions were taken by the Intelligence Community that actually amounted to criminal violations of federal law.
The course taken seemed right to Church as the Committee’s Chairman. One might imagine he understood there was great pitfall involved with criticism the work of Intelligence Community, however, Church never hesitated. By Risen’s account, Church was in fact persistent in his pursuit of the matter. He would show historic strength in his greatest moment. Risen did not indicate that Church had wasted any of the Committee’s valuable time rooting around in extraneous matters. Church stayed focused on his task.
This essay is not a book review. Instead, it is a literary insight essay providing meditations of Risen’s The Last Honest Man. In brief, a literary insight essay’s purpose is to express a readers feelings and ideas about a literary work. It is a journey of introspection. In this essay, greatcharlie’s insights are delimited to a discussion of occasional rogue behavior, abuses of law, by members of the US Intelligence Community. The book is remarkably suggestive with respect to contemporary times. Such an edict surely requires examination. In this essay, readers may come upon aspects of issues or view new angles of the discussion they may not have not recognized or perhaps would not have considered after reading the book
In previous times, one might have supposed the understanding, acceptance of what Founding Fathers who authored the US Constitution defined as the unalienable rights of life liberty, and the pursuit of happiness were sacrosanct. However, one might be able to comfortably conclude today that far less importance is given to those rights upon which the country’s soul and existence was once firmly based and upon which the US public’s expectation and requirement for the good governance of the democracy has its roots. What seemed so certain about the once lauded strictures–as a sampling, the Bill of Rights, the first 10 amendmens of the US Constitution–that would guide the country perpetually, is far less sure today than ever before. There are laws, but very often justice for the people is much harder to find. Breaches of regulations of the US Intelligence Community against ordinary citizen, not responsible for any wrongdoing, must not only be examined but vigorously pursued. Si quid novisti rectius istis, candidus imperti; si nil, his utere mecum. (if you can better these principles, tell me; if not, join me in following them.)
Meeting of the Members of the Church Committee prior to several hearings in autumn (above). Some Members of Congress in 1975 would likely have been more inclined to be dismissive of an investigation of the Intelligence Community than give serious attention to it. The Intelligence Community’s leadership could only hope that matters concerning its operations would be handled by the Church Committee with the same delicacy. The Congress for years had failed for years to put a leash on the Intelligence Community. Consequently, it ran off on its own in the world. Nothing but the foreign opposition, stood in its way. As for what remotely sufficed for “oversight” before the Church Committee was set up, information on Intelligence Community activities was curiously gleaned from the organizations’ directors by senior Members of both the House and Senate Armed Services Committees. They would meet with the directors to occasionally chin-wag likely on the latest activities, resources, personnel, latest activities, troublesome spots, and accomplishments. In those times, save the Congress and the free press, the US public would be assuredly have been kept in the dark regarding the government’s actions in the province of intelligence. The means today by which the US public is kept equally abreast of the Intelligence Community’s activities as then is not as certain. To that extent, what aided the Church Committee’s cause was the fact that certain elements of the national newsmedia, far less then than today, were nevertheless the best and only fount of information about the US Intelligence Community’s performance.
The Church Committee, known formally as the Senate Select Committee to Study Government Operations with Respect to Intelligence Activities established on January 27, 1975. Open sessions were held in September and October of 1975, but incisive research was conducted throughout that year. Prior to the Church Committee, there had not been any formal Congressional oversight process for what became the US Intelligence Community for nearly 30 years. The CIA was established in 1947, and the NSA was organized in 1952.The FBI has been around since 1924. The intelligence activities of a White House domestic surveillance program and the Internal Revenue Service were also probed. Following up on information reported in a December 22, 1974 New York Times article authored by investigative journalist Seymour Hersh, there was plenty sitting in the vaults of the Intelligence Communityfor the Committee to investigate. It was not mere tittle-tattle.
Some Members of Congress in 1975 would likely have been more inclined to be dismissive of an investigation of the Intelligence Community than give serious attention to it. The Intelligence Community’s leadership could only hope that matters concerning its operations would be handled by the Church Committee with the same delicacy. The Congress for years had failed for years to put a leash on the Intelligence Community. Consequently, it ran off on its own in the world. Nothing but the foreign opposition, stood in its way. As for what remotely sufficed for “oversight” before the Church Committee was set up, information on Intelligence Community activities was curiously gleaned from the organizations’ directors by senior Members of both the House and Senate Armed Services Committees. They would meet with the directors to occasionally chin-wag likely on the latest activities, resources, personnel, latest activities, troublesome spots, and accomplishments.
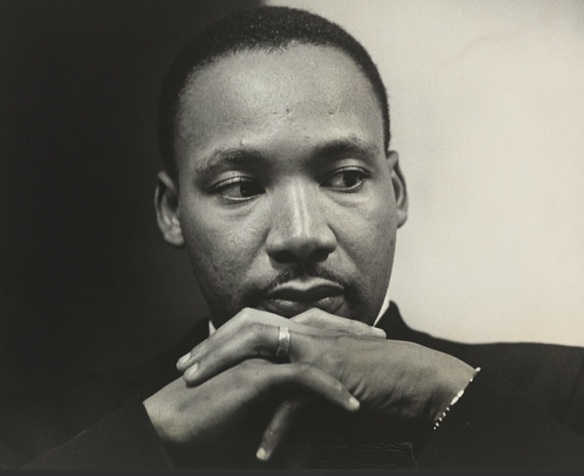
There was a danger that as a result of the Church Committee coming off the heels of the Vietnam War, the violent response to the Civil Rights Movement, the assassinations of Martin Luther King , Jr., Senator Edward Kennedy, and the earlier assassination of US President John Kennedy, Watergate, and the country’s continued disfunction on race, equality for women, and gross inequities in wealth establishing large divisions in social class, enabling poverty. the Intelligence Community would not be used as a depository for the ills of US foreign and national security policy.
Omne ignotem pro magnifico. (Everything unknown is magnificent.) In the old-fashion, out-moded sense, the US public at the time appreciated the services provided by its case officers and special agents, had possessed an sense of obligation to its Intelligence Community. However, ultimately, the Intelligence Community is beholding to the people who expect and deserve its unwavering fidelity.
When evidence of Intelligence Community wrongdoings and abuses became overwhelming, much changed on all fronts. The US had to confront the truth about itself if it was reach the heart of the matter.The Committee soon discovered that there was no possibility to the limits of the Intelligence Community’s operations. It was clearly capable of any fantastic outrage. There was a certain method to the eccentric madness of the Intelligence Community. What was discovered was all outside of the common. There was no outlier so to speak. Nothing revealed could have dare been called trivial. It was essential for the Church Committee Members to be put in the full picture. A priority appeared to be to gain a sense of the scale of those activities. This matter went much deeper than originally supposed.
It required life experience to understand what might be possible, to explore with an open-mind, all that would likely stand much of what Church Committee Members believed to be known on its head. To accept all that was being exposed in Church’s Committee would require one to possess a mind that could view it all with a mixture of imagination and reality. At the same time, many Church Committee Members and staff served overseas during World War II, as well as in the Korean War and in the Vietnam War were not mystified by any of it. It was about killing, death. Nothing was beyond their comprehension. As with other Committee members, Church examined the Intelligence Community’s activities burdened with a rational frame of mind. There were difficulties, but there would always be difficulties.
True, what was done was done. However, there was the chance to prevent the furtherance of such activities, crimes and halt any additional damage to the reputation and standing of the US worldwide . The US is a constitutional federal republic, meaning its government is based on a Constitution which is the supreme law of the country and both citizens and their governing officials are bound to follow the rules established in that Constitution. The Intelligence Community’s actions overseas over the years fell under the jurisdiction of the countries in which the occurred. However, their actions against US citizens inside the US fell under federal and state law. Remarkably, an extraordinary number of operations conducted by Intelligence Community members and other government organizations against domestic targets were discovered.
In those times, save the Congress, as well as a free press, the US public will be assuredly kept in the dark regarding the government’s actions, particularly in the province of intelligence. The means today by which the US public is kept equally abreast of the Intelligence Community’s activities as then is not as certain. To that extent, what aided the Church Committee’s cause was the fact that certain elements of the national newsmedia, far less then than today, were nevertheless the best and only fount of information about the US Intelligence Community’s performance. At least for a generation or two, not too long afterward, certain services of the Intelligence Community would remain dark organizations in the minds of many conscientious US citizens. There has been nothing of such consequence concerning the Intelligence Community beyond the IranContra Affair in which its activities have been put from and center for the US public. As a news story in present times, Church Committee findings unlikely would be of interest to the overwhelming majority.
William Colby, Director of the CIA from 1973 to 1976 (above). Once the Church Committee came prying, the Intelligence Community’s leadership and even White House under US President Gerald Ford appeared to become unsettled. The Intelligence Community’s leadership knew exactly what had been transpiriing in their organizations over the years. A reasonable assessment, completely unbiased, would be that under the strictures of US law, particularly on the domestic front, much of it was wrongful. To that extent, the Intelligence Community’s leadership, particularly the CIA’s leadership, knew members of the Church Committee would light on them once they had the opportunity to become read in on information available and actiually see and handle some of the recherché tools and gadgets the Intelligence Community had developed. Given how the hearings were organized, Intelligence Community executives and senior managers would have a considerable measure of control over their organizations’ fates and their own careers as would provide testimony as key witnesses before the Church Committee in both open and closed sessions. Whatever the Intelligence Community’s leadership hoped to accomplish, particularly with regard to minimizing the shock to the US public over each fantastic outrage revealed, surely failed if disproving newly hatched fears about the Intelligence Community was one goal, their efforts were not successful. Contrary to whatever public relations benefit the Intelligence Community’s leadership may have been hoping to garner as result of the hearings, the Intelligence Community’s reputation instead was decisively sullied. Yet, years later, it is clear that whatever resulted from the Church Committee Hearings hardly held fast. The way that the US public thought about not only the government and the Intelligence Community and also the ability to hold it accountable, would shift, opening the door to abuses that would have been beyond the Church Committee’s wildest imagining.
Once the Church Committee came prying, the Intelligence Community’s leadership and even White House under US President Gerald Ford appeared to become unsettled. The Intelligence Community’s leadership knew exactly what had been transpiriing in their organizations over the years. A reasonable assessment, completely unbiased, would be that under the strictures of US law, particularly on the domestic front, much of it was wrongful. To that extent, the Intelligence Community’s leadership, particularly the CIA, knew members of the Church Committee would light on them once they had the opportunity to become read in on information available and handle some the recherché tools and gadgets the Intelligence Community had developed.
From their view, circumstances of the time, the Cold War, the Modern Age, surpassed the use of ordinary ways and means to defeat threats and assure policy aims. They expoused that extreme circumstances required extreme action. Much more was constantly being required to meet ends covertly. Despite the rather widespread disapproval of its actions, the Intelligence Community’s leadership never believed the use of “ramped up” tactics, techniques, and procedures was not a crime. Through there use, the Intelligence Community could fight adversaries by means other than war to safeguard US national security.
That explanation–that alibi–would not have a steadying effect on the US public, many of whom had been made quite concerned after learning from news media reporting of the open sessions of the Church Committee how the government, honorable and powerful, had been behaving in their name. Again, there was mostly disappointment among the people. A fearful mood had gripped some. If it were only a smattering of odd incidents, any audacious thinking and action perhaps might have seemed slightly tolerable. That by no means was the case.
The Church Committee Hearings were a moment at time in which the Intelligence Community’s leadership would been behooved to guard against self-deception and delusion to avoid becoming too far a field. However, their conviction over everything the Intelligence Community did, however, was so unwavering that one might imagine a private response among some executives and senior managers was ironically to question the loyalty of Church Committee members. The pretense within the Intelligence Community’s leadsrship was that their organizations were “something above”,” something better”, than the rest of society and thereby they were entitled to do things outside US values, principles, and laws.
Given how hearings were organized, Intelligence Community executives and senior managers would have a considerable measure of control over their organizations’ fates and their own careers as they would provide testimony as key witnesses before the Church Committee in both open and closed sessions.
If the Intelligence Community’s leadership had any thoughts of avoiding hearings, the Church Committee would brook no denial. Forced to go through the investigative process, they might have left the door open in their minds to the hope that the Church Committee’s findings would allow for the suggestion of a rationale for the behavior of their personnel and all the transpired over the years. They might have hoped to hear a plausible explanation that would circle around notions of the ubiquitous and ceaseless Communist threat posed by the Soviet Union, the Eastern Bloc countries,, and the People’s Republic of China to the US, its allies and friends, and other democracies worldwide.
A figurative pirate’s chest of the strange, unusual technologies and maccabre tactics, techniques procedures, and methods was unlocked and opened wide. It was trove of horrors. To the overwhelming majority of US citizens who gave their attention to the Church Committee hearings, all that was discovered felt, to turn a phrase of the era, very un-American. Risen describes Church Committee revelations on assassinations targeted at Cuban President Fidel Castro in Cuba, Congolese President Patrice Lumumba, and South Vietnamese President Ngo Dinh Diem. There were others. He reports on the CIA’s MKULTRA program.and the use of LSD. and it’s domestic surveillance program, HTLINGUAL. He tells the shocking story of the FBI’s surveillance and harassment of Martin Luther King, Jr. and other US activists under COINTELPRO operations. The CIA contacted an organized crime figure, Johnny Roselli, to act as an intermediary to elicit the assistance of Chicago organized crime boss Sam Giancana, to coordinate CIA efforts to assassinate Fidel Castro with the Mafia. This list barely scratches the surface.
There was a sense of revulsion among Committee members and staff. Each Committee Member may have felt something private, very intense, very off putting about matter. Some might say that many of Intelligence Community lurid activities reflected a loathing of the human race. Seemingly, it was the organization’s preferred way to have others to perceive it. The Church Committee did not really warm to any of those who testified. The Intelligence Community’s leadsrship was not always well-collected while offering testimony. Still, among those Church Committee Members who may have felt disgust over the deeds of the Intelligence Community they had funded generously, there was no intention of allowing anger and grief conspire to create a blindness that might interfere with their vital work.
Whatever the Intelligence Community’s leadership hoped to accomplish, particularly minimizing the shock to the US public over each fantastic outrage, surely failed. If mitigating newly hatched fears about the Intelligence Community was one goal, their efforts were not successful. Contrary to whatever public relations benefit the Intelligence Community’s leadership may have been hoping to garner as result of the hearings, the Intelligence Community’s reputation instead was decisively sullied. Yet, years later, it is clear that whatever resulted from the Church Committee hearings hardly held fast.. The way that the US public thought about not only the government and the Intelligence Community and also the ability to hold it accountable, would shift, opening the door to abuses that would have been beyond the Church Committee’s wildest imagining.
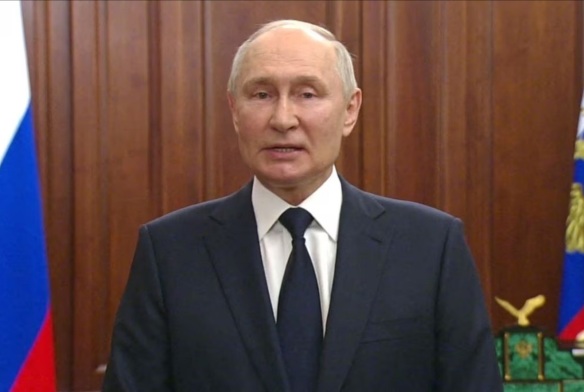
Surely, nothing uncovered by the Church Committee was lost upon the Intelligence Community’s opponents overseas. Their opponents overseas were tough and numerous. However, it seems elements of the US Intelligence Community thought of themselves as being tougher, and sought to be rougher still. It is doubtful that the Soviet Union, the Eastern Bloc countries, and the People’s Republic of China saw or heard anything too shocking or surprising. The Church Committee’s findings were unlikely music to their ears regarding the international front. Clearly, the US was active clandestinely and covertly overseas in a big way. On the domestic front in the US, however, the situation was likely viewed as much better by adversarial foreign intelligence services. News of the Intelligence Community’s history of operations against political targets very likely indicated to the Intelligence Community’s opponents that it was flush with so much cash that it could divert resources and manpower to those efforts.
Although it was not broached in Risen’s book, those political diversions may have provided enough reason for their foreign intelligence services to sense they were often operating with impunity in the US. Resources and manpower were not just diverted to that mission, but dedicated to it through multiple programs. Conceivably, that may have encouraged the Soviet Union, Eastern Bloc countries, and the People’s Republic of China to increase their presence and efforts in the US. The Soviet spymaster of Komitet Gosudarstvennoy Bezopasnosti (the Committee for State Security) or KGB, Oleg Kalugin, indicates in his memoirs that the 1960s and 1970s were heady, fruitful times for Soviet and Eastern Bloc intelligence operations inside the US. (SEE greatcharlie’s April 30, 2020 post entitled, “Book Review: Oleg Kalugin, The First Directorate: My 32 Years in Intelligence and Espionage against the West (St. Martin’s Press, 1994)”) It would have been almost impossible for the Intelligence Community to know the totality of what foreign intelligence services might have been successfully collecting at the time until new political, economic, or financial information allowed some unexplained upper hand or scientific or technological advances would crop up that evinced tell-tales of its origins and that it had been stolen.
Risen explains Church worked after the Committee Hearings to establish Intelligence Community oversight. Steps included the development of the Foreign intelligence Surveillance Act (FISA) of 1978 and creation of the Senate Select Committee on Intelligence on May 19, 1976 and the House Permanent Select Committee on Intelligence on July 24, 1977.
James Angleton, Chief of CIA Counterintelligence from 1954 to 1975, at the Church Committee Hearings. A figurative box of the strange, unusual technologies and maccabre tactics, techniques procedures, and methods was unlocked and opened wide. It was trove of horrors. To the overwhelming majority of US citizens who gave their attention to the Church Committee hearings, all that was discovered felt, to turn a phrase of the era, very un-American. Risen describes Church Committee revelations on assassinations targeted at Cuban President Fidel Castro in Cuba, Congolese President Patrice Lumumba, and South Vietnamese President Ngo Dinh Diem. There were others. He reports on the CIA’s MKULTRA program.and the use of LSD. He tells the shocking story of the FBI’s surveillance and harassment of Martin Luther King, Jr. and other US activists under COINTELPRO operations. The CIA contacted an organized crime figure, Johnny Roselli, to act as an intermediary to elicit the assistance of Chicago organized crime boss Sam Giancana, to coordinate CIA efforts to assassinate Fidel Castro with the Mafia. This list barely scratches the surface. During his testimony at the Church Committee, Angleton was pressed on the CIA’s domestic surveillance program, HTLINGUAL. It was sensed at the time that Angleton had not been completely forthcoming with Committee Members.
Without pretension, what greatcharlie relates in the following discussion is completely true and accurate to the best of its knowledge and belief. The information is simply laid out. There is no insistence that readers accept it. It is what it is.
After the September 11, 2001 terrorist attacks on the US, practically all curbs of the psyche and actual policy and legal parameters against abuses were not observed to the letter–somewhat overlooked–by the Intelligence Community in favor of a “go get ’em” attitude and offensive posture against “the enemy”. The priority became getting results: killing and capturing terrorists; uncovering and thwarting terrorist plots; destroying terrorist networks; and, seizing terrorist assets. The practice nearly became “anything goes.” The mainstream newsmedia in the US was supportive of just about everything done and a very vocal US public demanded further retribution. The emotional response of the US public was certainly understandable, however, most were abysmally ignorant of the Intelligence Community’s activities were overseas, literally on the high seas, and domestically. Among US public there are those who, even after being introduced to actualities, are unable to would hardly shake their views how their government can often operate. Today, only a fraction might take a firm interest in the misdeeds, violations of rights under the Constitution, or even larceny and outright violent crimes committed by the Intelligence Community. It is likely the case for members of the US public that as long as the Intelligence Community’s actions do not directly effect them or their own, there is little to be concerned about. To go a step further, some members of the US public may not be willing to accept that rogue elements of the Intelligence Community and their contractors would engage in surveillance and direct acts against innocent US citizens. Nevertheless, it happens, as Risen’s book makes it very clear.
The Global War on Terror has not ended. However, US President Joe Biden has reorganized resources and manpower in the over two decades long ubiquitous fight. Fewer airstrikes are ordered in fewer countries. US counterterrorism forces appear to be operating overseas in lesser numbers. The tempo of their operations has decreased. One would expect those decisions and others have had a correlative impact of ratcheting down the Intelligence Community’s use of resources and manpower. Looking a bit further on its tasks, no greater evidence of the Russian Federation’s potential for military aggression exists at the present than the Ukraine War. Yet, relative threats posed by the Russian Federation to the US and its interests has lessened. The degree of inefficiency and albeit incompetence that has been displayed by the Russian Federation Armed Forces and the intelligence services in the prosecution of operations of or pertaining to the Special Military Operation that the Cold War fears of the untamable and indomitable “”Russian Military Bear” has since faded at bit.. However, concerning the People’s Republic of China, however, its intelligence services have displayed an acumen in their espionage activities within the US that has been seemingly beyond the capacity of US counterintelligence services to combat. US foreign intelligence operations in the People’s Republic of China also have not met with great success. In the aggregate, the People’s Republic of China has delivered wrenching blows against the US.
The point here is that with relatively reduced threats against some opponents and barely a modicum of success against espionage directed from the People’s Republic of China foreign intelligence services in the US, some unscrupulous individuals in the organizations of the Intelligence Community may feel a “greater flexibility to do other things” undistracted by real work upon which they could fully focus their minds and hone their “skills”. Thereby, in an odd and unhealthy, and criminal twist, they appear to have shamefully preyed upon the average US public. Rogue members of these organizations–and there always have been a few– have engaged have engaged in this behavior for years, but happens not with similar frequency. They generally engage in their wrongful acts well-below the radar. It is awful to accept that a few personnel of the US counterintelligence services, including not so trustworthy contractors they call upon, to knowingly use the exquisite technical resources of the US and tactics, techniques procedures and methods to crush ordinary citizens who have no interest in doing anything against the US. (On this matter, greatcharlie writes not from study, but rather from personal experience as an innocent target of such wrongful and incredibly costly activities.)
The rogue federal officers and contractors have their own reasons for turning to villainy and own reasons for selecting their victims. The victims names may have been found on some innocuous list within the rogue federal officers organizations. Through wrongdoing, the names are apparently transferred to an active list of targets for the rogue federal officers and contractors to prey upon. Rogue federal officers and contractors will claim to have legitimate cause for their actions them. Warrants from “helpful” judges presiding on the Foreign Intelligence Surveillance Court (FISC) will be provided based on those claims, allowing electronic surveillance, physical search, and other forms of investigative actions for foreign intelligence purposes. (The FISC was established by Congress in the aforementioned FISA.) More importantly, the warrants will allow the rogue federal officers and contractors to increase available financial resources for activities against their innocent victims.
Needless to say, cellphone calls, texts, emails of victims are monitored. Letters and other missives are intercepted, extracted from, and occasionally inserted into, the victims mail deliveries. Electronic devices to monitor the victims in their own homes are used. Cable television and high speed internet services are weaponized for use as monitoring equipment. The technologies may have changed, but this practice of monitoring resembles that used against Martin Luther King, Jr. when he was, as noted earlier, the target of a federal surveillance and “dirty tricks” program. Yet, far much more, not relayed here, is done along this track. The individual’s personal life, finances, property, could are targeted. Doors will be closed to employment, association with social and professional groups, membership in organizations. Recognition and awards for achievement and excellent will be denied. Family members and friends will also face attacks designed to separate them from the individual or destroy them. Every effort will be made to shun the victim from society.
To gnaw a bit further on the surveillance of a victim, as a standard practice that task is performed through the use of manpower on the street. The personnel of a contractors are used mostly for this purpose. Some are employeed to engage in electronic surveillance. To use manpower on the street in a very robust way, contractors, albeit errantly, will hire ordinary individuals from the US public to assist them. Greater budgets allowed once FISC warrants are secured mean bigger operations. That permits exigent hires For rogue federal officers and contractors greater budgets through innovative ways mean greater wrongful operations,, but also the potential for increased financial gains for them. (In the past, waggish federal officers were sometimes heard to jest that such improper efforts perfectly allowed for the creation of a “second retirement” much better than the one their organizations were going to provide.) C’est comme ça.
It is rarely difficult to find exigent hires willing for usually modest, but sometimes exhorbitant payment–bribes–to zealously engage in surveillance activities and aggressive, even criminal acts at the behest of rogue federal officers and contractors. Most of the exigent hires only understand “spy work” through Hollywood depictions and exciting novels. Most are thrilled to live out “Walter Mitty” fantasies of being a spy as they disrespect, betray and bully the innocent! The ranks of citizen hires are inflated by the exigent employ of permanent and temporary residents, visitors, tourists, and undocumented immigrants as well. The visitor to the US will receive an unforgettable lesson on the meaning and nature of civil rights in the country courtesy of the rogue federal officers and contractors. Whether a citizen or visitor, the hires receive remuneration. Exigent hires are compensated immediately for their wrongful service. The payments are in essence bribes to encourage and to reward their violation of the law. If prospective hires take the unusual step of asking why such surveillance of the victim is necessary, the rogue federal officers and contractors will offer an apocryphal story that may shock, anger, or outrage the prospect concerning the victim, tell outright, ghastly lies about the victim’s character, or conversely set aside any wrongdoing or any threat posed by the victim and convince the hire that anything done will be to the victims benefit! Intriguingly, the latter actually works exceedingly well.
Exigent hires will invariably approach the surveillance of their innocent victim using the limits of their varied faculties. The results can be atrocious, shocking, and sometimes silly. Exigent hires can often be seen hiding behind pillars, jumping behind cars, and hiding their faces with their hands among a few things. As the vetting of hires is nonexistent, the dysregulated are often employed and they will often vent rage directly at the victim over false reports about them from rogue federal officers and contractors to relieve unbalanced levels of stress and frustration. Occasionally, participation is shamefully impelled not only by remuneration, but by racial, ethnic, religious, and gender prejudice. Those hires will indubitably make their offensive perspectives known to victims when walking by them or loitering near them. Evidence of how they manage racist and otherwise biased hires may offer an indication of whether the rogue federal officers and contractors harbor similar prejudices toward a victim. They can often develop a kinship with such odious individuals. On the odd occasion, one might unexpectedly observe the rogue federal officers and contractors communicating with them in plainview! Those hires surely receive opportunities for contracts and more chances to abuse a victim for payments. There is often a sense great importance and power that conspiring with “secret men” and “secret women” conveys to most hires, this can expectedly lead to hostility, aggression, and violence against an innocent victim.
Since none of the hires employed under these circumstances are not acting against actual officers or operatives of a foreign intelligence service or some other dangerous group, these exigent hires can act with relative impunity against victim. A victim’s response to the hires transgressions must not include acting physically. The rogue federal officers and contractors will use their standing and FISC warrants to ensure local law enforcement will arrest a victim and “friendly” prosecutors will secure fines or sentences against them. Such occurances have indeed been tragedies. Yet, the activities of the rogue federal officers and contractors will not stop even after causing that degree of harm. On s’en fout!
The exigent hiring of “operatives” by rogue federal officers and contractors is not always unsystematic. Some hires are offered contracts to encourage regular service against innocent victims. Often, contract hires are asked rogue federal officers and contractors to log their observations of victims via text or group chat. They often provide the information on what the victim is wearing, the number of the taxi in which the victim is riding, the direction the victim is walking or the activity in which the victim is engaged. (Interestingly, rogue federal officers and contractors always inform their hires of their victims whereabouts, yet they will often insist their hires log their “observations” of the victim by text or group chat. Other than creating activity for the hires, that work amounts to kabuki, hardly serving a useful purpose day-to-day when the rogue federal officers and contractors are watching the victim themselves. Maybe it is more a matter of keeping up appearances.
Some exigent hires are sought out because they are in a position to have opportunities for more than occasional contact with a victim. These “key hires” will,typically be associated with the victim’s personal and professional life, and the victim’s simple daily activities. A short list of such hires would typically include: neighbors; apartment building staff; contractors; locksmiths, municipal civil service workers of all types to include the police and emergency services technicians; dog walkers; taxi cab drivers; car service drivers; barbers; hairstylists; restaurant staff; pizza shop employees; coffee shop staff; street food vendors; conveniance store clerks; department store employees; luxury watch store employees; supermarket employees; car garage attendants; storage company employees; moving company employees; realty agency staff; funeral directors, movie theater staff, museum staff; performing arts center staff; elementary and secondary school staff; parents of elementary and secondary school students; elementary and secondary school students; visiting professors at nearby universities; sports book authors; content management system employees; bank branch employees; accountants; tax preparers; paralegals; lawyers; medical office administrative staff and technicians; physical therapists; doctors; court house staff; and, judges. (The actions of judges co-opted by the rogue federal offcers and contractors in an US court proceeding against a victim are typically so remarkably corrupt that greatcharlie assures they must be seen to be believed.) It is fascinating to observe just how many individuals are typically made privy to the rogue federal officers and contractors “secret operations” against innocent victims.
Through contact with such key hires, the rogue federal officers and contractors aditionally hope to receive information about the victim through “clandestine conversation”. Usually, they will insist these hires ask victims specific questions about themselves which is most often incongruous with the natter in which they might be normally engaged. The activities of those key hires, along with other hires who have contracts, are controlled through cellphone calls, direct texting, and group chat. Group chat is at the present the most unified way for the rogue federal officers and contractors to assemble and mass their hires to act upon a victim collectively. Essentially, hires are organized for “gang stalking” and out-and-out harassment–bullying. These hires are compensated usually at central locations in the vicinity of their activity: a parked car or a coffee shop.
Interestingly, with warrants from the FISC in hand, rogue federal officers and contractors can also make use of programs created for use by employees of specific service industries to surveil and act against targets of investigations. In New York City for example, a clandestine program–so called a covert program by officials–was developed by federal and local law enforcement and US intelligence services to use taxi cab and car service drivers to surveil and photograph targets when they are on the street and to engage them in clandestine conversations as passengers with the aim of “surreptitiously interrogating” them or passing disinformation to them. Remember, the victims are absolutely innocent, have no special information offer. So, insisting the taxi drivers engage in such a practice, certainly not as training, along with simply using the shed light upon the mental state of the rogue federal officers and contractors. Maybe it is again a matter of keeping up appearances. It is as plain as a pikestaff that the taxi and car service drivers are impelled by pecuniary interest and ego, certainly not intellect. Clearly, most of the drivers take on their “secret work” having received insubstantial educations overseas, possessing a limited vocabulary as English is usually a second language for them, being devoid of sophisticated conversational skills–being tactless, and not knowing what it means to be congenial. One can imagine how awkward, clumsy, and better than annoying their efforts at “clandestine conversations” usually are. Ironically, the drivers must rely upon the politeness and tolerance of the victim to perform their “clandestine” work while lacking any compunction over deceiving a victim or potentially causing them harm.
It might be worth noting that warrants from FISC also allows for the rogue federal officers and contractors to cooperate with members of foreign intelligence and security services of US allies stationed in the US. The officers of some foreign intelligence and security services will make their presence known to victims by behaving overly aggressively, with hostility, and even a threatening them. Indeed, they take on this barbaric posture even against US citizens living in their own country. Officers of somewhat more sophisticated foreign intelligence and security services may make it a point to have an attenuated presence. However, they may deliberately make themselves known if they have been tasked to ask questions of–softly interrogate–the target. Interestingly, that task invariably falls to female officers of the foreign intelligence and security services who, with male colleagues close by, will “noticeably” spend an ordinate amount of time studying the victim before moving in. Such activities fall under the category of transnational repression and are illegal. Foreign intelligence and security services of US allies are surely pleased to receive financial resources from their US counterparts for their cooperation. Warrants from FISC open the financial spigot for such funding. However, what is imaginably most important for the foreign intelligence and security services of US allies who might participate in such activities at the victim’s expense is finding a place for themselves at the “high intelligence roundtable” with the powerful US. Once again, rogue federal officers and contractors more than likely trigger this activity by foreign intelligence and security services stationed inside the US as a matter of keeping up appearances.
Attempts to co-opt a victim’s immediate family members and other relatives are also made by rogue federal officers and contractors. If successful, they will usually forever destroy the victim’s immediate family unit and separate the victim permanently from other relatives.
The definition of success among the Ancient Greeks was the full use of one’s powers along the lines of excellence. At a minimum, success for the rogue federal officers and contractors against their victims clearly has meant stripping them of anything resembling an ordinary life, completely restricting their liberties in a normal sense by standing between the victims contacts with others, and interfering with any effort to pursue happiness. The whole wrongful process can go on for years or at least as long as the victim lasts. Yet, very often the outcome desired by the rogue federal officers and contractors is far more sinister. The “stress response”, the flight or fight system, is triggered when mind and body are out of balance. When mind and body are out of balance, in stress mode, one is headed for health problems, disease, or breakdown. No organism can stand being in emergency mode all the time. The infliction of daily episodes of gang stalking and harassment can elicit heart disease, heart failure, and psychological disorders. Cases of suicide can also stem from a victims in ability to cope with strains too strong and too alien for “normal living” in an advanced industrial democratic society to countenance. Mere empirical observations of rogue federal officers and contractors actions and the results inflicted upon victims should reasonably assure one that there is not a shred of decency among them. Far more perverse actions are taken against victims. Plainly, the rogue federal officers and contractors have even acted in a variety of ways to cause a victim’s death.
As mentioned, the exigent hires and contract hires of the rogue federal officers and contractors are generally more concerned with how much money they will receive. Typically, hires will hardly notice, or even look to see on their own volition, if the victim were suffering physically or psychologically in some discernible way. As a combination of the hires’ “low-vibrational” character and their receipt of regular abhorrent reports from the rogue federal officers and contractors about the victim usually meant to infuriate their hires or even amuse them, there is generally no empathy shown by hires for the victim. The victim is not recognized as a human being. The victim is seen only as a commodity. Noticeably, hires are quite deliberately directed and bound as a collective through a form of mind control. From the prostitute and drug peddler to the doctor and state court judge, the rogue federal offcers and contractors get their hires to do exactly what they want them to do. The reality is there is no professional side to involving US citizens and so many others in the wrongful–illegal–surveillance and possibly the criminal homicide of anyone, especially an innocent victim. In their own criminal way, the rogue federal officers and contractors are destroying the fabric of the society.
Victims of rogue federal officers and contractors have no voice. The few who would make reports of their maltreatment and entreaties for justice are stifled by the corrupt. Through the use of their standing with law enforcement and judicial systems, FISC warrants, and long exercised technical ways to block a victim’s communications, it is assured that the victim’s pleas will go unheard. Many victims are so despaired by trying and failing to successfully report their mistreatment and circumstances surrounding it that they are led to either very quietly or very publicly self-destruct.
As suggested earlier, it is easy enough for those in the US public who cannot accept corruption and murderous criminality on such great scale among corrupt members of the US security services and their contractors and some will surely to find comforting ways to dismiss it or outrightly rebuke it. Yet, those who would accept this reality may be unwilling to speak against it. The number of other government officials in the organizations who may discover others acting corruptly and may wish to report or to investigate such criminality would be few as the consequences of their detection might be retribution in the form of daily attacks on the job equal or worse than those suffered by the innocent victims.
Leaders of organizations can be changed in response to revelations of wrongdoing at the senior level and within the rank and file. However, a subsequent change in leadership to that could lead to the rejuvenation of such vengeful, aggressive thinking and actions against the previously targeted inedividual found guiltless, incident free will be ordered. The individual’s personal life, finances, property, could once again be targeted. Doors will be closed once again to employment, association with social and professional groups, membership in organizations. Recognition and awards for achievement and excellent once again will be denied. Family members and friends not co-opted by the rogue federal officers and contractors once again will face attacks designed to separate them from the individual or destroy them without fail. Victims will once again be shunned by the society. During the new episode, the most devastating psychological and physiological attacks upon the individuals–by then a few years older and likely less interested in struggling against a tide a wrongdoing–would be launched by authorities with far greater intensity, to achieve their destruction or even deaths through suicide or violence so dearly wanted by others through the original effort. Ironically, the rogue federal officers and contractors who assisted in organizing and managing the individual’s destruction originally, will very likely have retired from their federal security service by then to enjoy the fruits of their wrongdoing. However, others would doubtlessly rush forward to take their place. Où va-t-on à partir de maintenant?
This is in some small part the actual state of affairs for many victims of rogue federal officers and contractors at the moment. It is a whole world invisible to the ordinary citizen. As explained earlier, there is no insistence that anything discussed here be accepted by readers who are unfaniliar with it all. Nevertheless, everything presented is true and can be easily substantiated with the cooperation of honest and thoughtful law enforcement officials. (Note: All that is discussed concerning the mistreatment of citizens by rogue federal officers and contractors is based on the author’s personal experience!) One might suppose that for those who may be interested in how surveillance is conducted on the street level in the US, this discussion may prove instructive. It is unlikely lost upon readers that “one” who might desire to penetrate domestic surveillance activities in the US, not too much would be involved with becoming a “contract hire”. Once onboard as a hire, one would potentially have access to details about the daily surveillance activities of some US intelligence service or law enforcement organization, such as what organization was currently tasked with, who exactly is being targeted, where the target is acting, and who the organization’s street “operatives” are. What could be accomplished by “one”, one in a hypothetical case being a foreign intelligence officer or a team of officers and operatives tasked with the mission of infiltrating surveillance activities of a US intelligence service or law enforcement organization, must be left to the imagination.
One possibility might be the regular successful “collection” of vital information to protect their country’s foreign intelligence operations inside the US. One can only guess how difficult it would be to launch successful counterintelligence operations against a wily foreign intelligence sserviceoperating inside the US when it knows everyday where its opponent’s officers and operatives are and who and what they are looking at. Perhaps something of the kind is already happening on some scaleg. For that reason, for more than a theory, on-going surveillance operations as discussed here, either sanctioned by authorities or wrongful conducted by the rogue federal officers and contractors, should be immediately rolled up, audited, and assayed. Perhaps doing any of that would be too bothersome. (Curiously, the average individual in the US public may not accept that such wrongful behavior by rogue federal officers and contractors occurs, however foreign intelligence services surely have no doubts about what transpires.) Born Jacques Anatole François Thibault, known as Anatole France (April 16, 1844-October 12, 1924) was a French poet, journalist, and novelist. Considered in his day as the ideal French man of letters. He was awarded the 1921 Nobel Prize in Literature in recognition of his literary achievements. In Le Petit Pierre (1918), ch. XXXIII, he wrote: “De toutes les définitions de l’homme, la plus mauvaise me paraît celle qui en fait un animal raisonnable.” (Of all the ways of defining man, the worst is the one which makes him out to be a rational animal.)
Martin Luther King, Jr. (above). When King was the victim of FBI’s surveillance and harassment under its COINTELPRO operations, he had committed any federal crimes and was not a threat to US national security. He was an innocent US citizen. To that extent, actions taken against him by Intelligence Community organizations once uncovered by the Church Committee were shocking and surprising. In previous times, one might have supposed the understanding, acceptance of what Founding Father’s who authored the US Constitution defined as the unalienable rights of life liberty, and the pursuit of happiness were sacrosanct. However, one might be able to comfortably conclude today that far less importance is given to those rights upon which the country’s soul and existence was once firmly rooted and upon which the US public’s expectation and requirement for the good governance of the democracy has its foundation. What seemed so certain about the once lauded strictures–as a sampling, the Bill of Rights, the first 10 amendmens of the US Constitution–that would guide the country perpetually, is far less sure today. There are laws, but very often justice for the people is much harder to find. Breaches of regulations of the US Intelligence Community against ordinary citizen, not responsible for any wrongdoing, must not only be examined but vigorously pursued.
Seared in the minds of the authors of the US Constitution, the Founding Fathers, were the extraordinary sacrifices made by thousands of Colonists before and during the Revolution. Attendant to that were acts of tyranny leveled upon colonists by authorities in the Kingdom of Great Britain. There was usually much suffering dealt by the British Army to the rebellious in territory controlled by the British Empire. Methods used by the professionals of the British Army for the purpose of assuring the Kingdom’s grip on the Empire’s many lands overseas were tried and true. Given the that, the victory of the American Colonists, with assistance from France, was spectacular and almost supernatural. The tyranny resulting from the imposition of coercive power by the Kingdom of Great Britain was a manifestation of what was intrinsic in mankind: the desire to control others for self-interest. The despotic intrusion of ones will upon another compelled in some. The Bill of Rights, the initial 10 Amendments of the US Constitution are in part responses of the Founding Fathers. to egregious injustices under which Colonists suffered much of which was intended to break any sense of unity among them.
It is greatcharlie’s firm belief that few in the US public–indeed, relative to the size of the population and to include officers of the court–are aware of the contents of the Bill of Rights and their meaning. There is the real possibility that many in the US may have no interest at all in the matter. Rather than simply utter the term, Bill of Rights, which for many may amount to empty words, greatcharlie offers the concisely authored first 10 amendments of the Constitution passed by Congress on September 25, 1789 and ratified on December 15, 1791.
The First Amendment states: “Congress shall make no law respecting an establishment of religion, or prohibiting the free exercise thereof; or abridging the freedom of speech, or of the press, or the right of the people peaceably to assemble, and to petition the Government for a redress of grievances.”
The Second Amendment states: “A well regulated Militia, being necessary to the security of a free State, the right of the people to keep and bear Arms, shall not be infringed.”
The Third Amendment states: “No Soldier shall, in time of peace be quartered in any house, without the consent of the Owner, nor in time of war, but in a manner to be prescribed by law.”
The Fourth Amendment states: “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.”
The Fifth Amendment states: “No person shall be held to answer for a capital, or otherwise infamous crime, unless on a presentment or indictment of a Grand Jury, except in cases arising in the land or naval forces, or in the Militia, when in actual service in time of War or public danger; nor shall any person be subject for the same offence to be twice put in jeopardy of life or limb, nor shall be compelled in any criminal case to be a witness against himself, nor be deprived of life, liberty, or property, without due process of law; nor shall private property be taken for public use, without just compensation.”
The Sixth Amendment states: “In all criminal prosecutions, the accused shall enjoy the right to a speedy and public trial, by an impartial jury of the State and district wherein the crime shall have been committed; which district shall have been previously ascertained by law, and to be informed of the nature and cause of the accusation; to be confronted with the witnesses against him; to have compulsory process for obtaining witnesses in his favor, and to have the assistance of counsel for his defense.”
The Seventh Amendment states: “In Suits at common law, where the value in controversy shall exceed twenty dollars, the right of trial by jury shall be preserved, and no fact tried by a jury shall be otherwise re-examined in any Court of the United States, than according to the rules of the common law.”
The Eighth Amendment states: “Excessive bail shall not be required, nor excessive fines imposed, nor cruel and unusual punishments inflicted.”
The Ninth Amendment states: “The enumeration in the Constitution of certain rights shall not be construed ttho deny or disparage others retained by the people.”
The Tenth Amendment states: “The powers not delegated to the United States by the Constitution, nor prohibited by it to the States, are reserved to the States respectively, or to the people.”
It must be noted that under the Fourteenth Amendment, which concerns civil rights–as well as Senators, Representatives, and the public debt, citizens in the US, born or naturalized, and other individuals living in the US are entitled to equal protection under the law of the US and the State in which they reside and no person shall be. deprived life, liberty, or property, without due process of law under either jurisdiction.
Two centuries after the Bill of Rights were ratified, power can still corrupt. In the country the Founding Fathers constructed, led by a government formed of the people, for the people, and by the people, the aforementioned intrinsic negative impulses in mankind could nevertheless manifest within those who were members of the citizenry themselves. Despite swearing to an oath to support, protect, and defend the US Constitution and the solemn compact between government and the people, various episodes of corruption have taken their place in the country’s history.
Sojourner Truth was a 19th century African-American abolitionist and activist for civil rights, women’s rights, and alcohol temperance. Truth was born into slavery in Swartekill, New York, but escaped with her infant daughter to freedom in 1826. Sojourner Truth is known for saying “The truth is powerful and will prevail.” The truth will “prevail.” That is as may be. However, without some preconcerted, energetic effort to make certain the truth is heard, understood, and accepted by all who are reasonable and rational, it will unlikely have an impression and be unappreciated. Only a precious few open-minded individuals, following the law and holding firm to their beliefs, spiritual or philosophical, will hold firm to the truth.
Reportedly, the writer, professor, political activist, Nobel laureate, and Holocaust survivor, Eli Weisel, once explained God created man because He loves stories: Weisel would cite the Chasidic tale of the Baal Shem Tov. Accordingly, when misfortune threatened his community, Tov would venture into a certain part of the forest to meditate. There he would light a fire and say a special prayer. In consequence, misfortune would be averted miraculously. During a later time of peril, a despondent Rabbi Israel of Rizhyn addressed God as follows: “I am unable to light the fire. I do not know the prayer; I cannot even find the place in the forest. All I can do is to tell the story: this must be sufficient.” It did suffice, and God saved His People. Dum spiro spero. (While I breathe, I hope.)
By Mark Edmond Clark